This post was a direct result of a request from one of my readers. I hope that this post will explain VMware networks a bit more and how they fit into a production network.
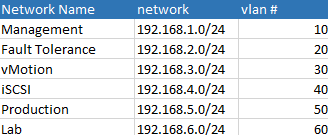
To begin I’d like to review how a VMware ESXi server might have its virtual switches and port groups setup to connect to a physical switch. Here is a list of networks that we’ll be working with.
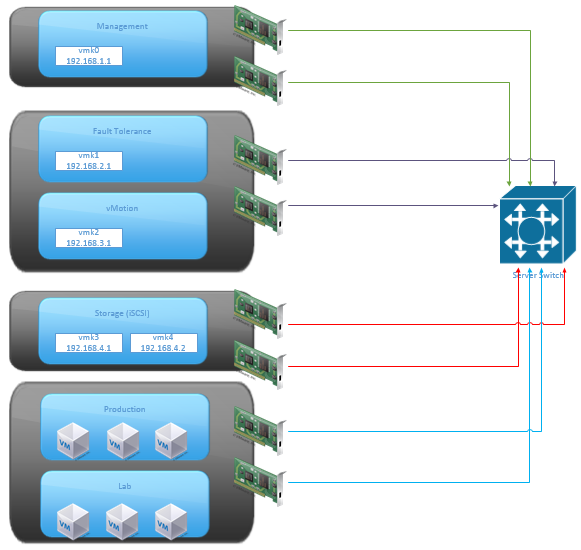
Below, I show the port groups for each network, the physical adapters that might be setup, and a physical server switch that the ESXi host might connect to. (You should always have multiple physical switches for redundancy but for brevity I’ve omitted this in the design,)
The last virtual switch contains two port groups. Production and Lab port groups contain only virtual servers and no vmkernal ports.
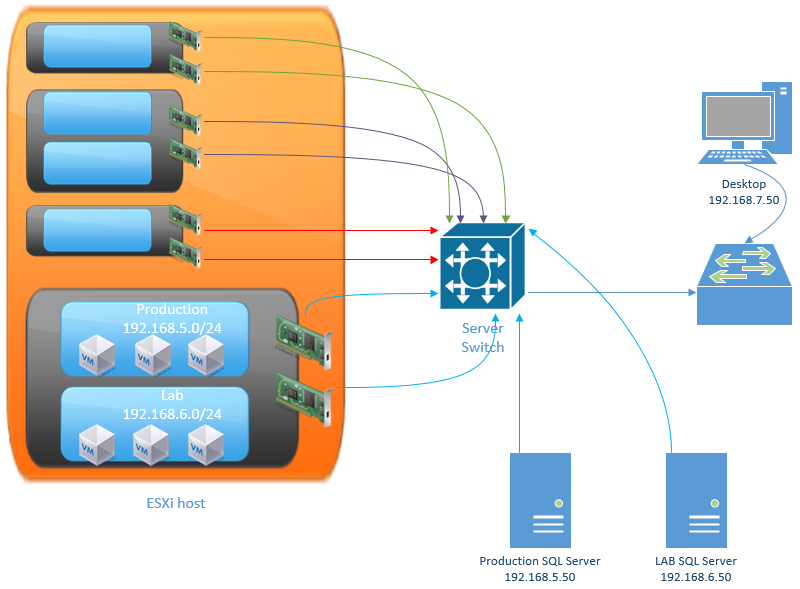
Now that we’ve got an idea how how a single ESXi hosts has been setup, we can reproduce the same configuration for multiple hosts so I won’t go into details on that. Instead, let’s look at what the network might look like with clients and some physical servers. I’ve omitted some of the ESXi information we just covered.
From the diagram we can still see the Production and Lab port groups but I’ve added the network they are on as well, in order to show that they are on the same LAN segment as two physical servers “Production SQL Server” and “LAB SQL Server”.
The fact that some of the production servers are virtual and some are physical will have little to do with the network design. If you were to P2V the Production SQL Server, you could put it directly in the Production port group and keep the same IP Address.
Why use different networks at all?
You could create a single network such as 192.168.1.0/24 and put management, Fault Tolerance, vMotion, iSCSI, production, lab and client computers in it. This is possible to do, but shouldn’t be done for performance reasons. The more devices on a segment, the more chance for collisions which will cause re-transmits to occur and will slow down your network.
Another reason to not use a single network segment would be for security purposes. If different services such as iSCSI and management traffic are on different networks, it makes it easier to firewall the traffic based off the network ID.