A secured, remote connection to your data is a requirement for almost all network designs these days. Mobility, telecommuting and late night help desk calls have created an environment that needs to have access to the local network in a secure fashion. vCNS Edge can provide these services to your virtual infrastructure.
In previous posts, I’ve walked through installing vCNS Manager and installing vCNS Edge appliances. These are prerequisites to setting up SSL VPN on the VMware vCloud Network and Security appliance..
vCNS Edge Logical Setup
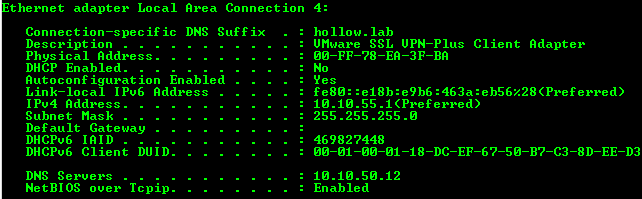
For the lab setup, there is a remote user machine, the vShield Edge Appliance, and the internal network that we’ll VPN into. We also create a pool of IP Address to be used by the VPN devices.
 vCNS Edge SSL VPN Configuration
vCNS Edge SSL VPN Configuration
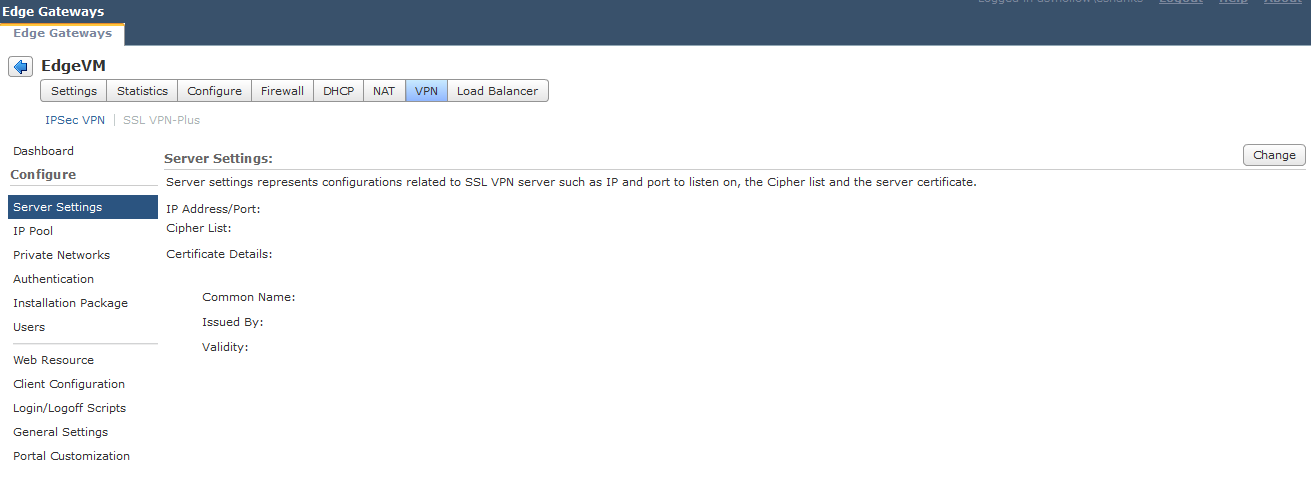
Go to your vCNS Edge appliance and navigate to the VPN Tab. From there click on the “SSL VPN-Plus” link.
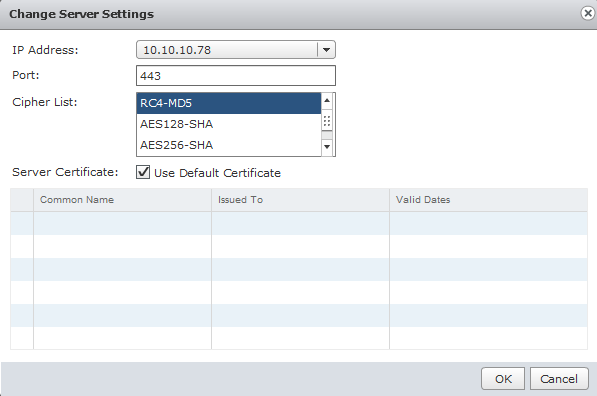
Under the Configure menu, go to Server Settings. Click the Change Button to modify the settings.
Select the external IP address of the appliance that you wish to use as the VPN endpoint. This doesn’t necessarily mean that this is the default external IP address of the gateway. You are allowed to change the port number if you wish, but the default is 443. You are also allowed to change the cipher list to something more secure. Since this is a lab, I’ve used RC4 and MD5. For production uses, it may be advisable to use AES and SHA. Lastly, you can use the default certificate or use a Trusted Certificate Authority. The latter would be recommended for a production environment.
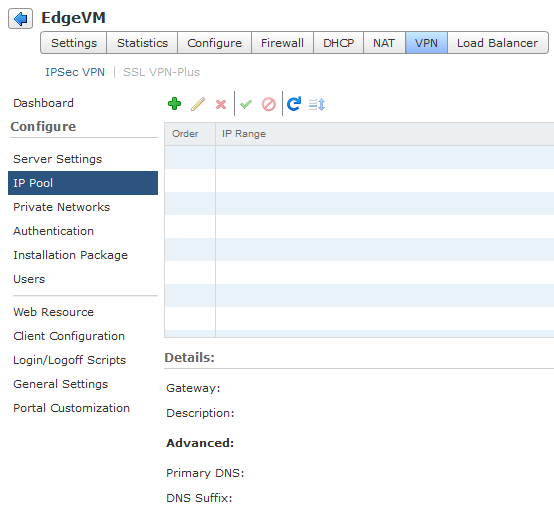
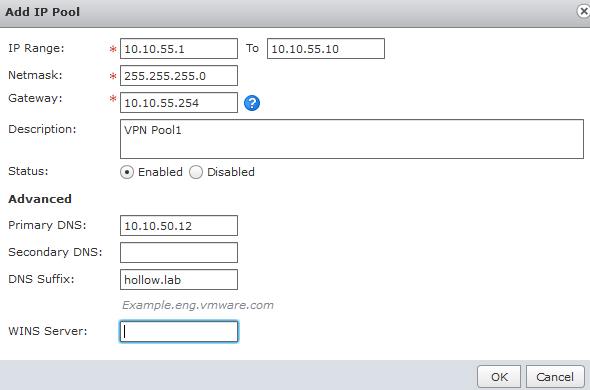
Next go to the IP Pools. Click the “+” sign to add a new Pool.
Add a new IP Pool. Enter a range of IP addresses that will be handed out to your VPN Clients. Enter a subnet mask and a default gateway address as well. The IP Range used should not be a range that is already on your vCNS appliance. Also, be sure to enter a subnet mask and a gateway. The gateway IP Address will be assigned as a virtual IP Address on the vCNS Edge appliance.
Lastly, it would be advisable to add a DNS Server and DNS Suffix here as well.
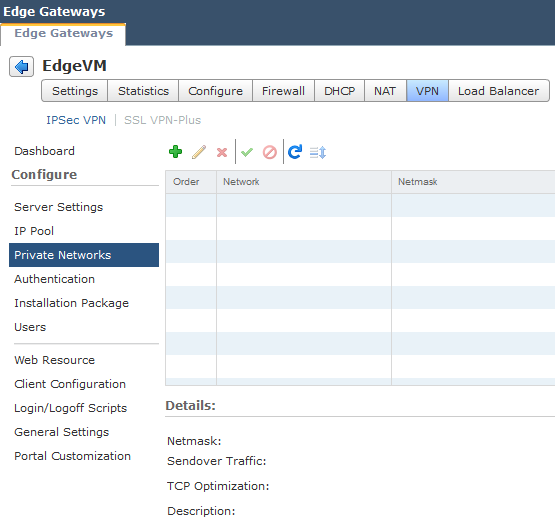
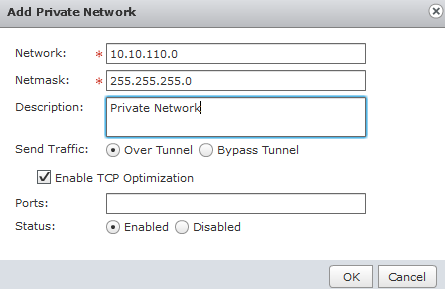
Next, you will go to the “Private Networks” section to configure what networks will be allowed to connect to through the SSL VPN. As expected, click the “+” button to add a private network.
Here, we add the internal network and the subnet mask. You’ll have the option to have the traffic encrypted or not by select the “Over Tunnel” option. The “Enable TCP Optimization” checkbox will enhance the performance of your TCP Packets. You can restrict the network access to specific port numbers by entering them into the “Ports” checkbox. If you don’t enter any, all ports are assumed.
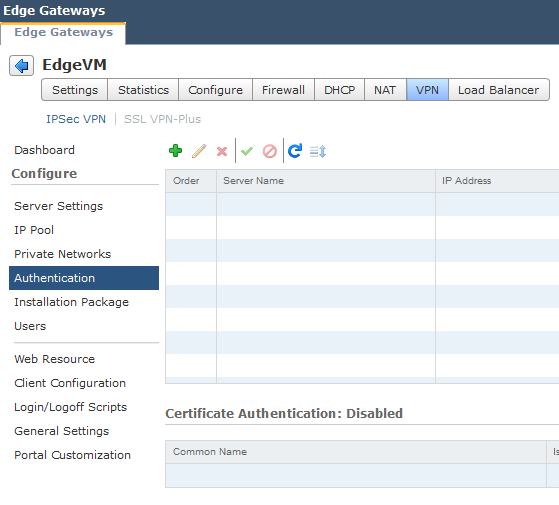
Next, we turn to authentication. Add an authentication method to your list of configurable items.
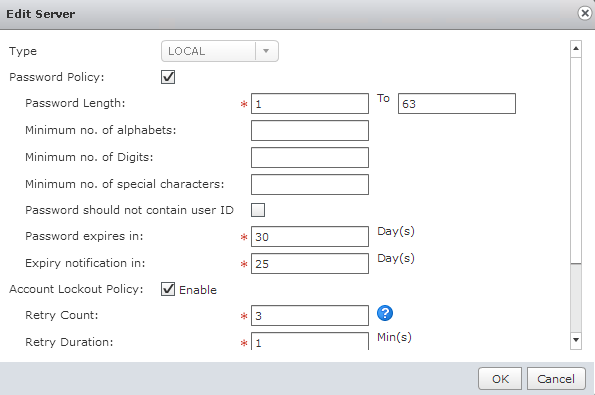
You can setup Active Directory, LDAP, local, Radius, etc. Again, since this is a lab, I’ve used a local authentication mechanism. If this is a production environment, AD or RADIUS might be more appropriate.
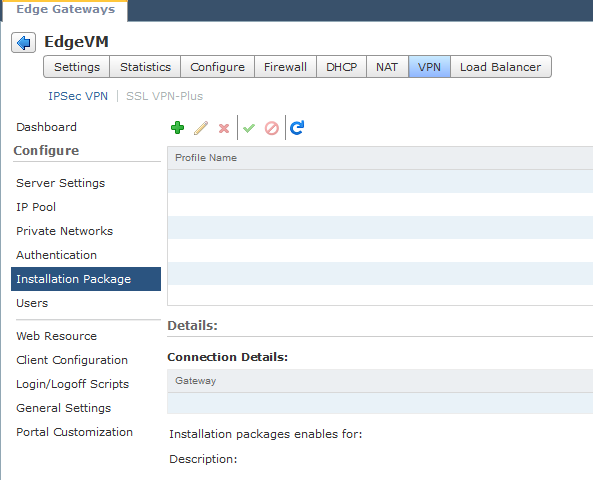
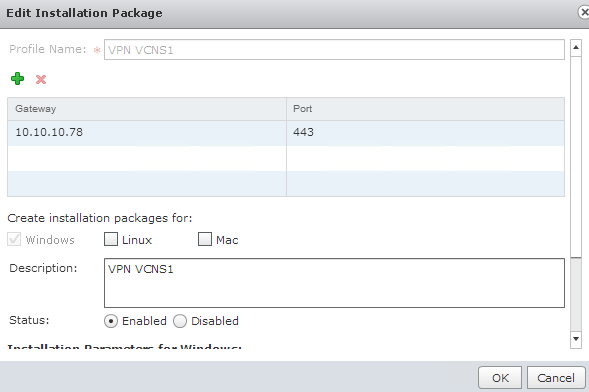
Now we need to add an installation package.
Enter a name and a description for the package. The more descriptive the better! The gateway IP Address should be the address of the outside IP address of the vCNS Edge appliance that you configured earlier. It should be noted that the IP address could be a public IP or public DNS address that has been NAT’d through another firewall on the edge of your physical network.
This package can be enabled for Windows, Linux, and Mac depending on your needs.
You will find additional parameters depending on what your organization is looking for. For instance, you want the VPN to fire up each time the machine starts up.
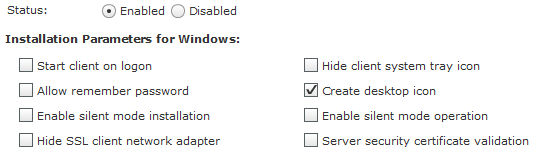
My last step is to add a local VPN user. If you’ve used AD or RADIUS, this may not be a necessary step.
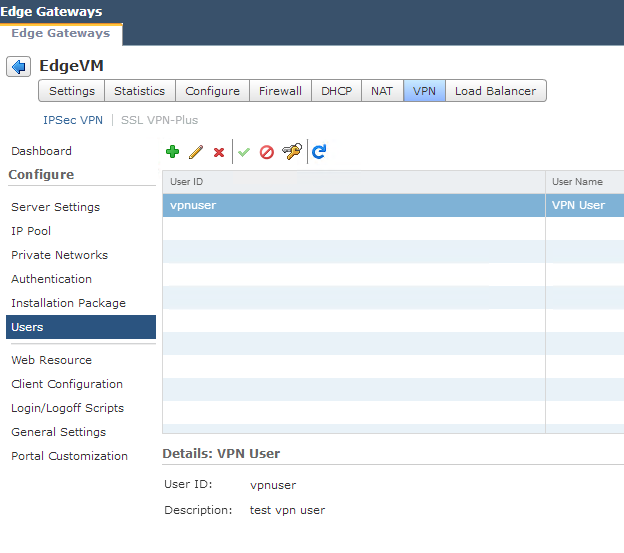
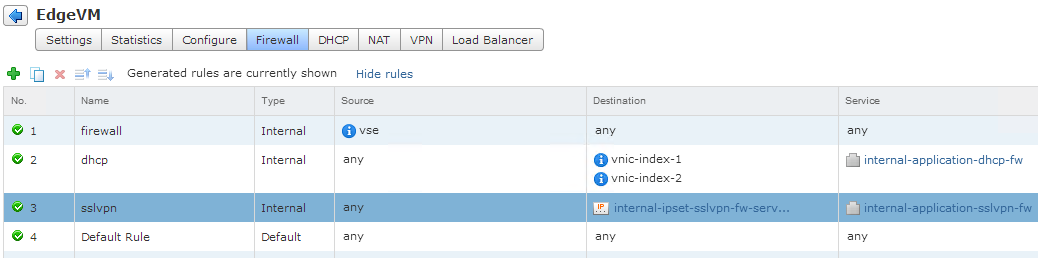
Firewall
Nothing needs to be configured here, but I wanted to show that a firewall rule is automatically added to the vCNS Edge appliance.
Install the VPN Client
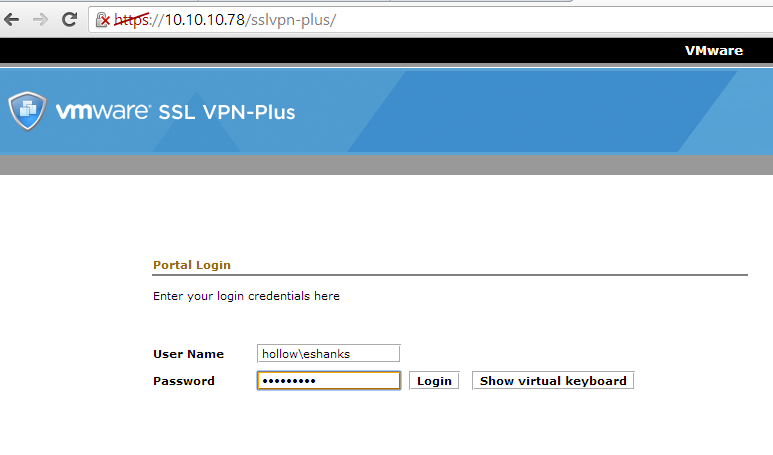
Open a web browser and go to the outside IP address of the vCNS edge appliance that you configured. You should be presented with a logon screen.
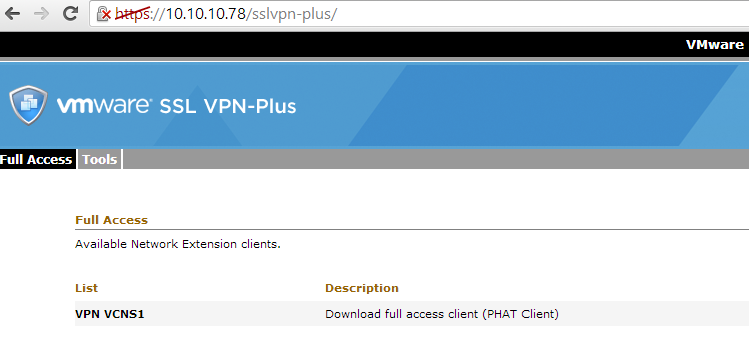
Once you login, you should see the ability to download the client. The client will install with the configured connection information. You may also see more than one client available if you’ve created multiple connections.
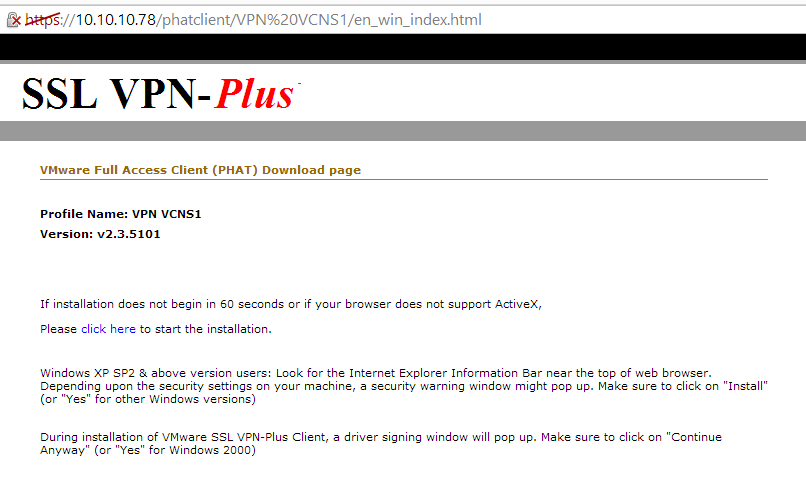
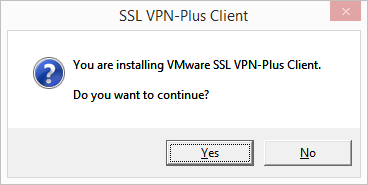
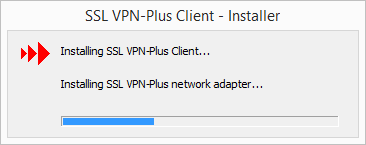
The installation process will start.
Connect to the VPN
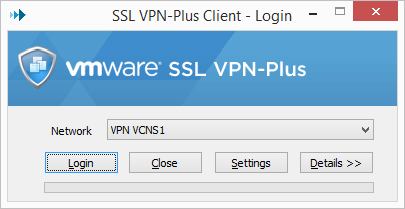
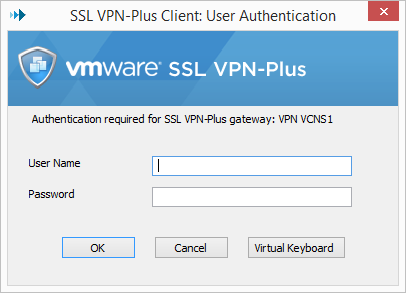
Launch the VPN Client, or if it was just installed, it should open immediately after install. Select the profile and Login.
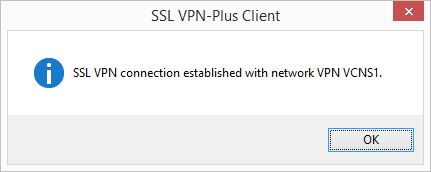
Once you enter a valid username and password, you should see the following message box and you’ll know you’ve been connected.
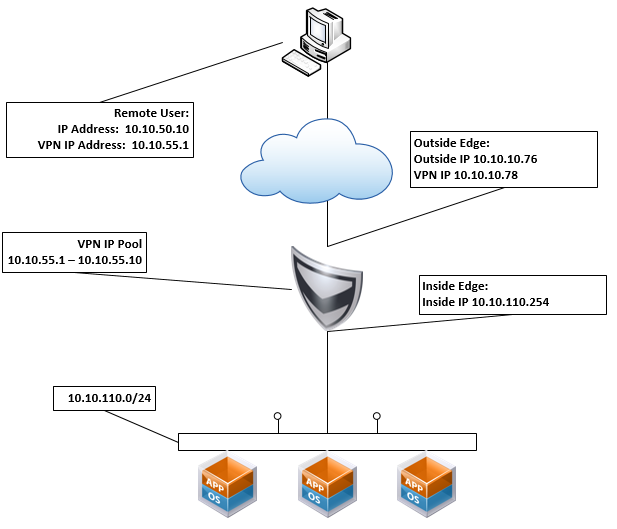
I ran an ipconfig command and it shows that I’ve got a 10.10.55.1 address as I should from the VPN Pool, and I can connect to the private network.
Summary
VPN is so important these days that any sort of edge appliance must have this capability. VMware has provided it in their virtual networking suite as well.