Home Lab SSL Certificates aren’t exactly a high priority for most people, but they are something you might want to play with before you get into a production environment. In part one of this series, I went over installing an Enterprise Root CA just to get us up and running. Again, be aware that for a production environment you should use an Offline Root CA and a Subordinate CA, but we’re in a lab and don’t need the additional layer of security.
Home Lab SSL Certificates aren’t exactly a high priority for most people, but they are something you might want to play with before you get into a production environment. In part one of this series, I went over installing an Enterprise Root CA just to get us up and running. Again, be aware that for a production environment you should use an Offline Root CA and a Subordinate CA, but we’re in a lab and don’t need the additional layer of security.
Configure Auto-Enrollment
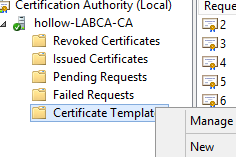
Open up the Certificate Authority MMC window from either Administrative Tools or via Server Manager –> Tools.
From here, we can right click on the “Certificate Templates” folder and choose “Manage”
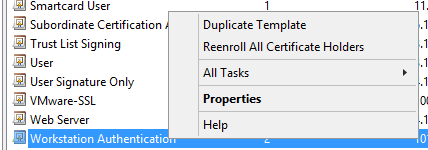
From here, we’ll look for the “Workstation Authentication” and choose “Duplicate Template”. (It’s not mandatory to do this, but I recommend doing it in case you need to go back to the original Workstation Authentication certificate template later on.) Give the new certificate template a name.
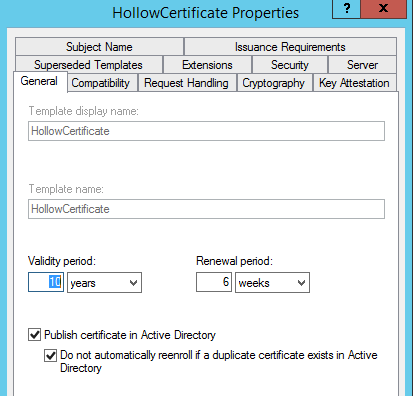
Next, we want to change some of the properties of this certificate. I’ve changed my Validity period to 10 years (again this is a lab and not production), and I’ve selected to publish the certificate in Active Directory.
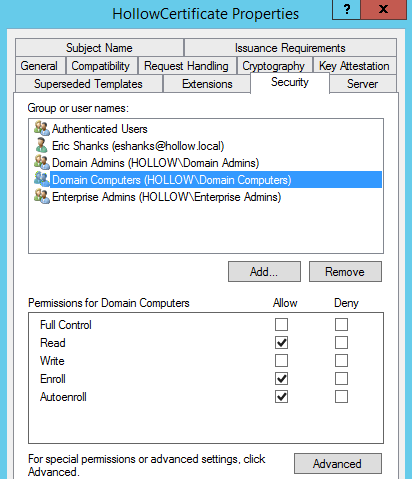
In the Security tab, I changed the “Domain Computers” permissions to read and autoenroll the certificate.
For the Extensions Tab i changed the Application Policies to include both Client and Server Authentication.
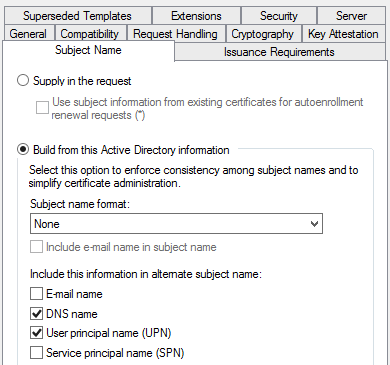
And in the Subject Name tab, added the UPN checkbox.
Save your changes.
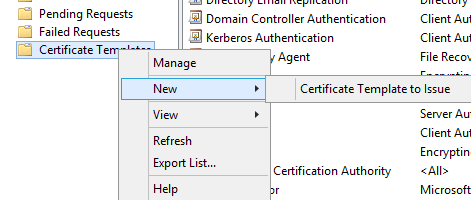
Lastly, once you’re done here, you can go back to the Certificate Authority MMC. Right click on the Certificate Template Folder and choose New–> Certificate Template to Issue. Then select the certificate template you just created.
Group Policy
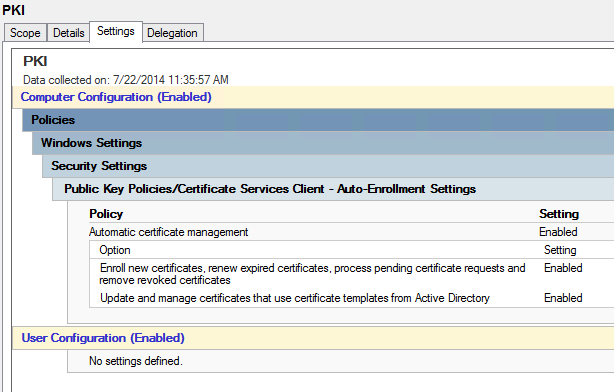
Now we need to have a way to tell the computers to automatically grab those certificates and install them as trusted certificates. Remember where we selected “Autoenroll” earlier on the certificate template? That doesn’t do anything until we configure a GPO to tell the computers to look for these certs.
Create a GPO (or use an existing one, it is a lab I suppose) and link it to an OU that should get these certificates automatically installed. Since this is a machine certificate, be sure to have it affect an OU with your computers in it if not the entire domain.
Results
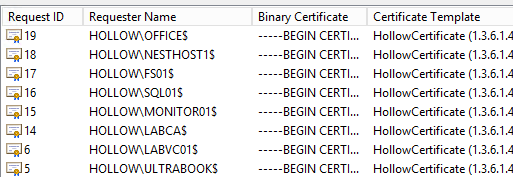
It might not take affect right away, but if you look in your Certificate Authority MMC under issued certificates, you will start to see some of them show up. If you want to test this quickly, you can run a gpupdate /force on a workstation to see if it shows up right afterwards.
Summary
We now have the Root Certificate Authority Installed and certificates are automatically being enrolled with all of our domain computers. This is an important first step to any Public Key Infrastructure. Stay tuned to future posts on how we can now leverage more certificates to protect our web servers.