An Azure network security group is your one stop shop for access control lists. Azure NSGs are how you will block or allow traffic from entering or exiting your subnets or individual virtual machines. In the new Azure Resource Manager Portal NSGs are applied to either a subnet or a virtual NIC of a virtual machine, and not the entire machine itself.
NOTE: At the time of this post, Azure has a pair of Azure portals, including the classic portal where NSGs are applied to a virtual machine, or the Resource Manager Portal where NSGs are applied to a VNic of a virtual machine.
Here are some notes that you should know about Azure Network Security Groups.
- The NSGs in Azure are Stateful. Meaning that if you open an incoming port, the outgoing port will be open automatically to allow the traffic.
- The default rules in a Network Security Group allow for outbound access and inbound access is denied by default. Access within the VNet is allowed by default.
- Like normal ACLs the rules are processed based on a priority.
- NSGs can only be used in the Azure region that it was created in.
- There is a soft limit of 100 NSGs per subscription and a soft limit of 200 rules per NSG.
Create NSG
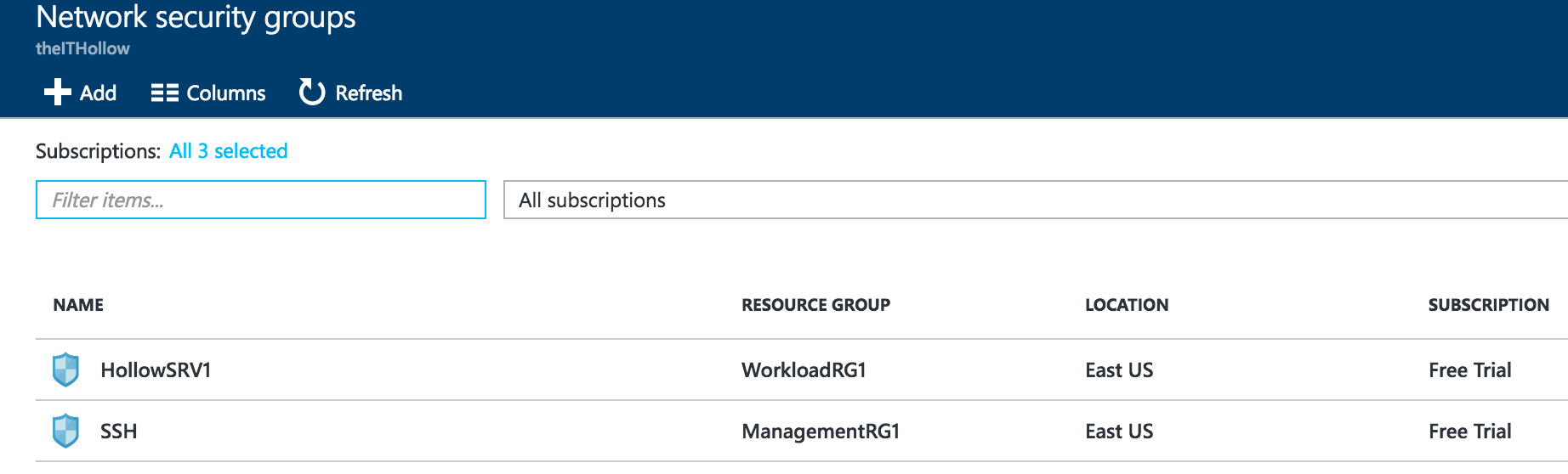
To create a network security group in the Azure Resource Manager browse to the “Network Security Groups” section in the ARM Portal. Click the Add button to create a new one.
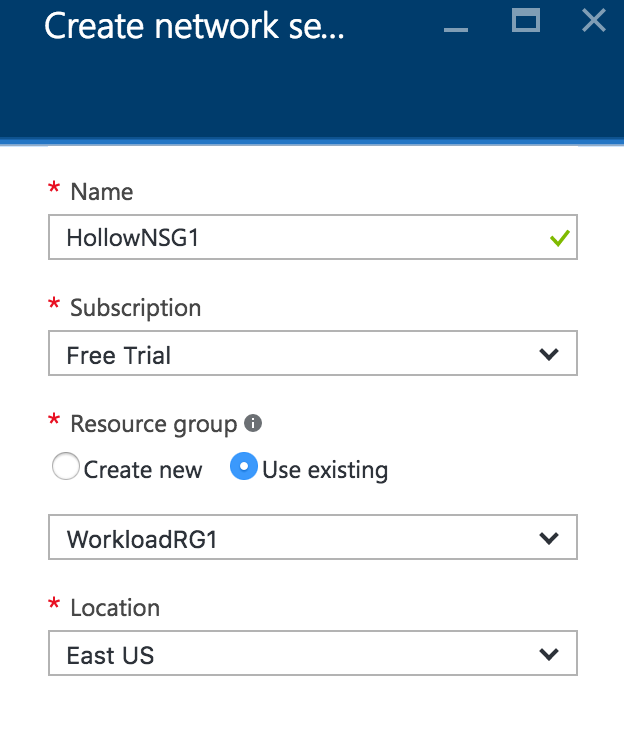
Give the NSG a name that will be descriptive for you and select the subscription that it will belong with. Be sure to use a descriptive name that won’t need to be repeated. An NSG name must be unique within the region. Then, select a resource group that it should belong to, or create a new one and then select the location or region. Remember that the resource group an be exported to deploy later on, so this way the access control lists can be deployed with the networks and virtual machines later on.
Create Rules
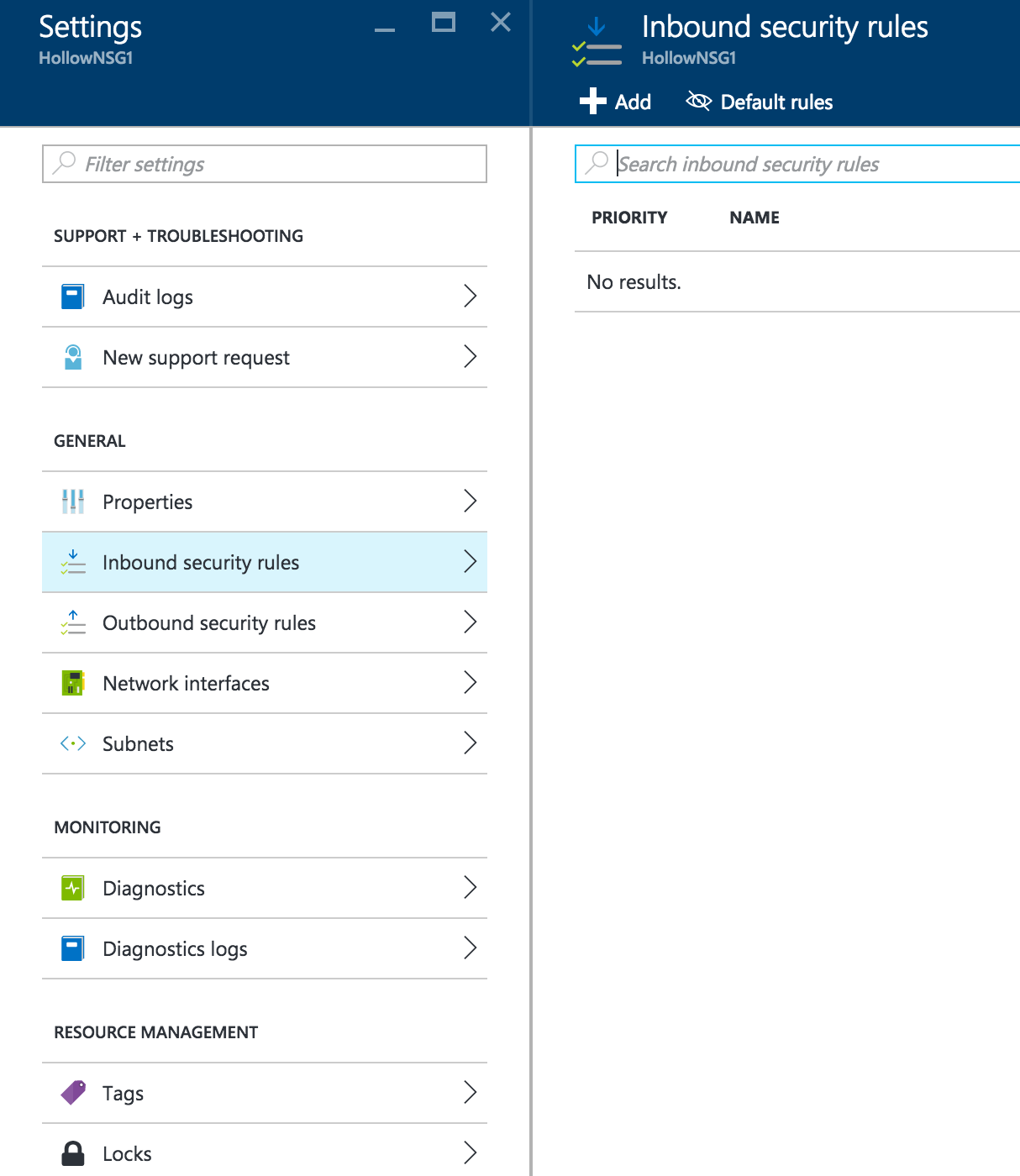
Once the NSG has been created, locate the NSG and go to the properties. Select either Inbound or Outbound security rules to add your customized rules. Click Add in the security rules page.
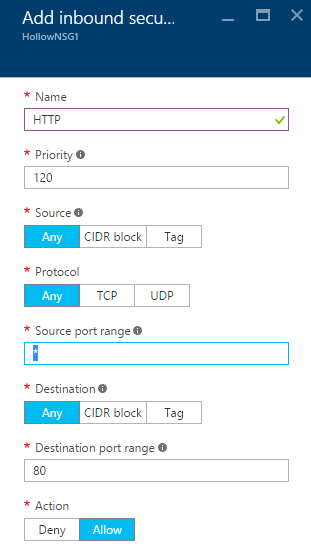
Give the rule a name typically a protocol, port or application name. Then give the rule a priority, remember the lower the priority the earlier in the process that it is evaluated. It’s also a good idea to leave space between rules so that you can insert new rules later. Don’t place your priorities at 10,11,12 because you may need to inject a rule between rules 10 and 11 but won’t be able to. A better method would be adding them as 10,20,30 so that there is room between them.
Next, select a source IP address, CIDR block or Azure Tag that the traffic will be coming from, assuming you’re doing an inbound security rule creation. Then select the protocol, source port range and the destination if you need to specify them. Lastly select the destination port range and either allow or deny the traffic.
Associate NSG
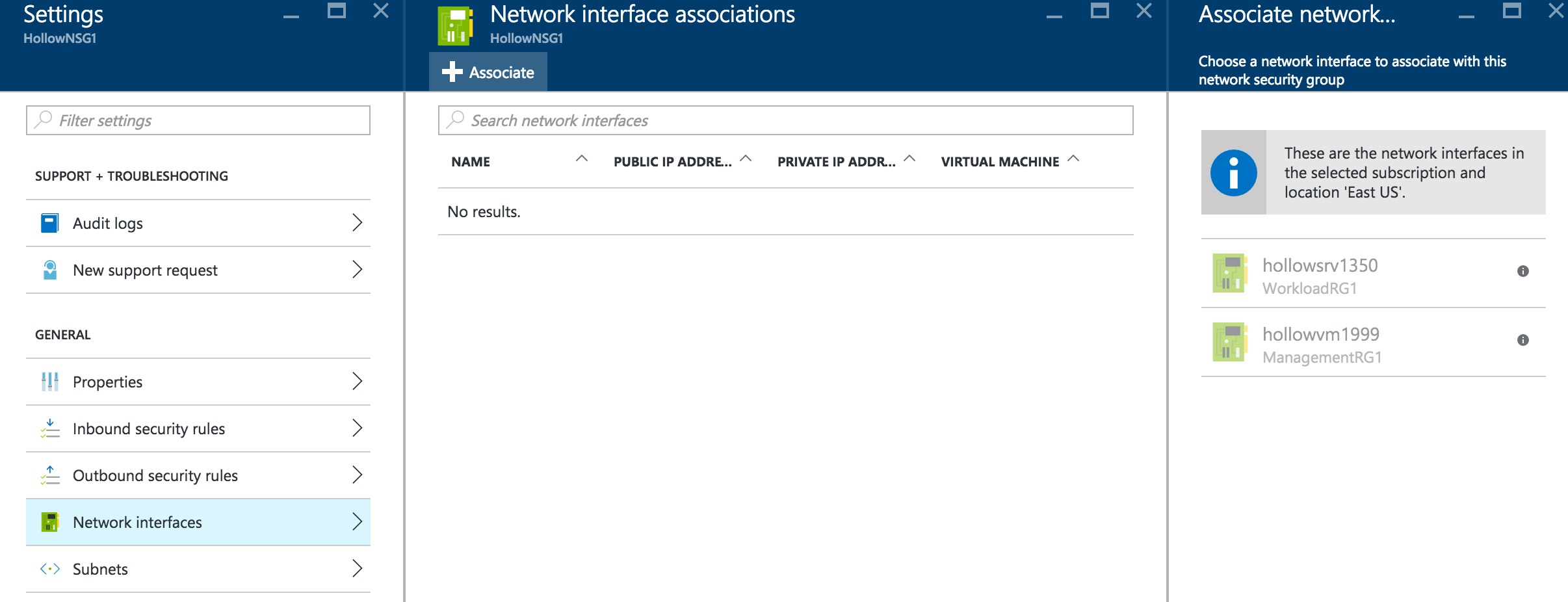
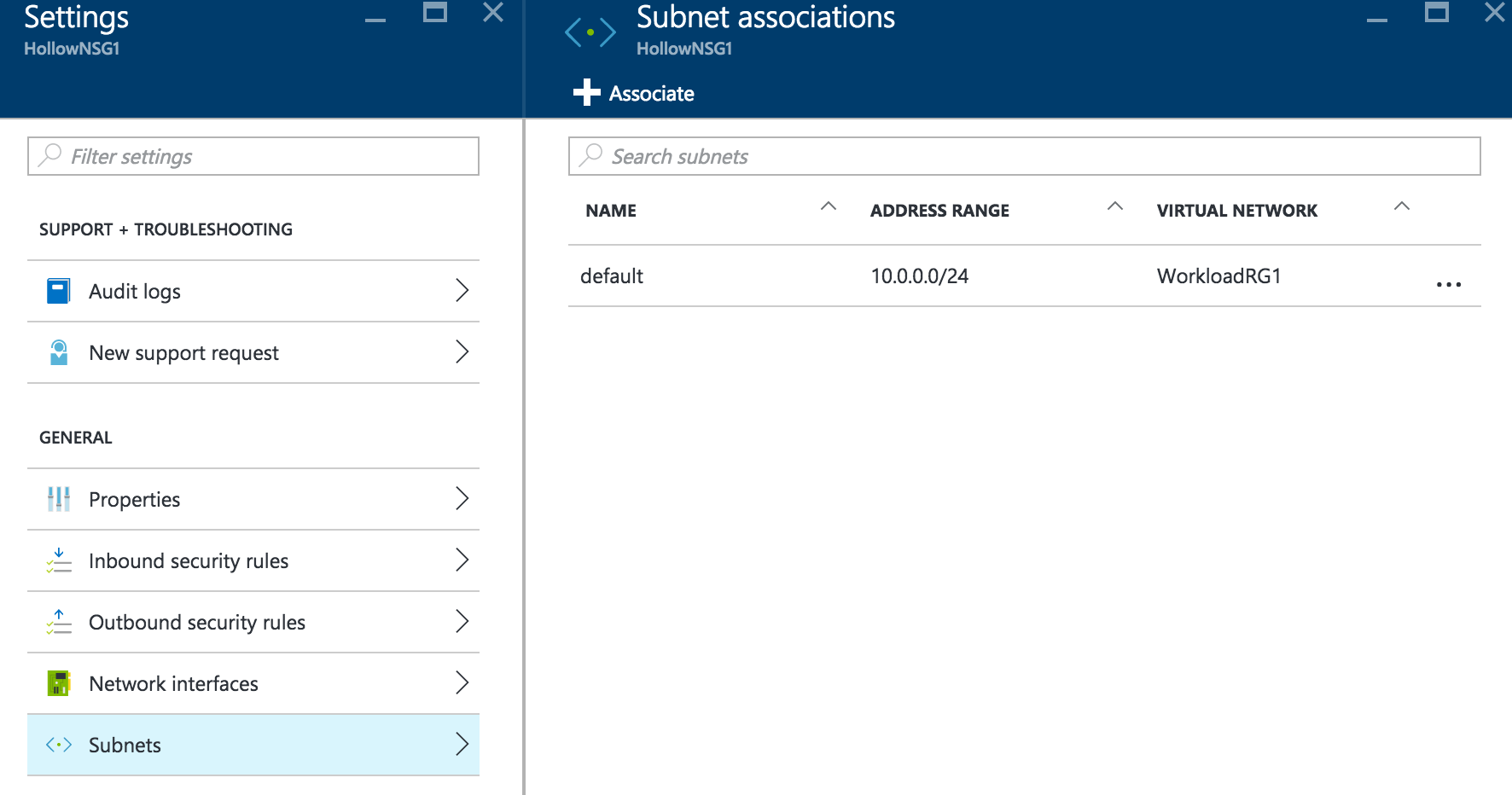
Once your Network Security Group is created and configured with your desired rules, you will associate that NSG with a subnet or network interfaces. Under the NSG properties select either the “Network interfaces” or “Subnets”.
If you’ve selected the Network interfaces you’ll click the “Associate” button to connect the NSG with a virtual machine NIC. That NSG will stay with the NIC so if you move it to a different virtual machine later, the NSG will follow it.
If you selected “subnets”, You’ll click the “Associate” button to connect the NSG with an Azure subnet.
Summary
Network security groups are in place to provide access controls to your virtual machines. These can be set at the subnet level to affect all of the virtual NICs attached in those subnets, or directly on a NIC themselves. These can be used to segment a tiered application, setup DMZs or just limit the access to the outside world so they should be planned out carefully for your new Azure networks.