Today Sysdig announced a new update to their Cloud Native Visibility and Security Platform, with the release of Sysdig Secure 2.4.
The new version of the Secure product includes some pretty nifty enhancements.
Runtime profiling with machine learning - New containers will be profiled after deployment to give insights into the processes, file system activity, networking and system calls. Once the profiling is complete, these profiles can be used to create policy sets for the expected behavior. Sysdig also offers a confidence level of the profile. Consistent behavior generating a higher confidence level whereas variable behavior would have a lower level.
Falco rule builder - If you’ve been using the open source version of Falco, you may really like the rule builder which places a neat UI for configuring these rules. The rule builder eliminates the need for deep knowledge of Falco expressions and just lets you get stuff done.
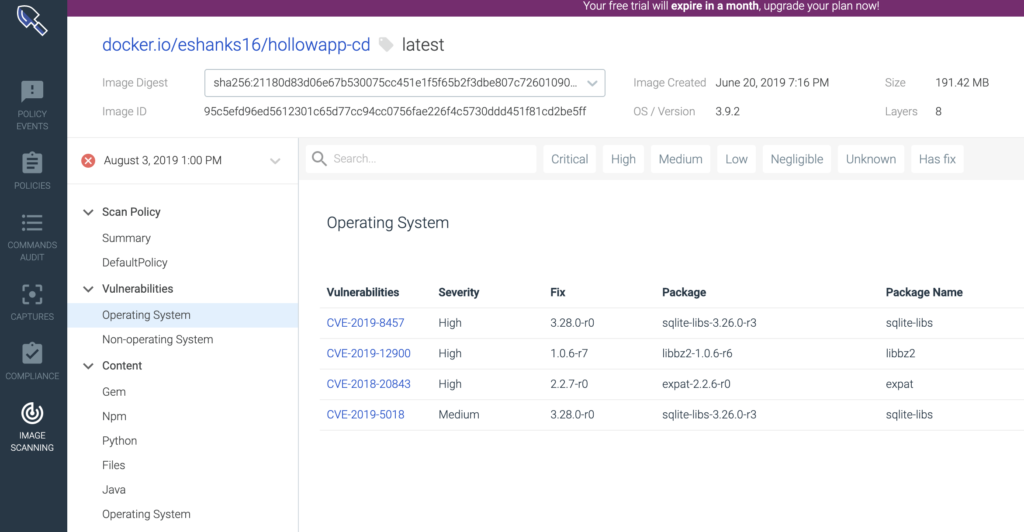
Additional vulnerability management - Sysdig already does vulnerability management, but now there are new features such as the vulnerability reporter where you can create custom queries for your environment. Also, the scan results UI gets a face lift and the alerting mechanisms were updated to notify users about CVE exposures and changes to images.
What is Sysdig Secure?
If you’re not familiar with Sysdig Secure and you’re running a Kubernetes cluster, you might want to check it out. https://sysdig.com/products/secure/
Sysdig Secure aims to help “secure” (you didn’t see that coming did you) your container environment by providing vulnerability management, compliance, runtime security and forensics tools. Sysdig Secure is the other half of their Cloud-Native Visibility and Security Platform. As you may recall, I tried out the Sysdig Monitor program and you can read that review here.
Secure Vulnerability Management
We have to harden our containers just like we harden our virtual machine images. Sysdig Secure can scan our containers within our registry, or through CI/CD to tell us about what nasty bugs we might have in our images. Luckily for me, my customized app is not mission critical or hold important data.
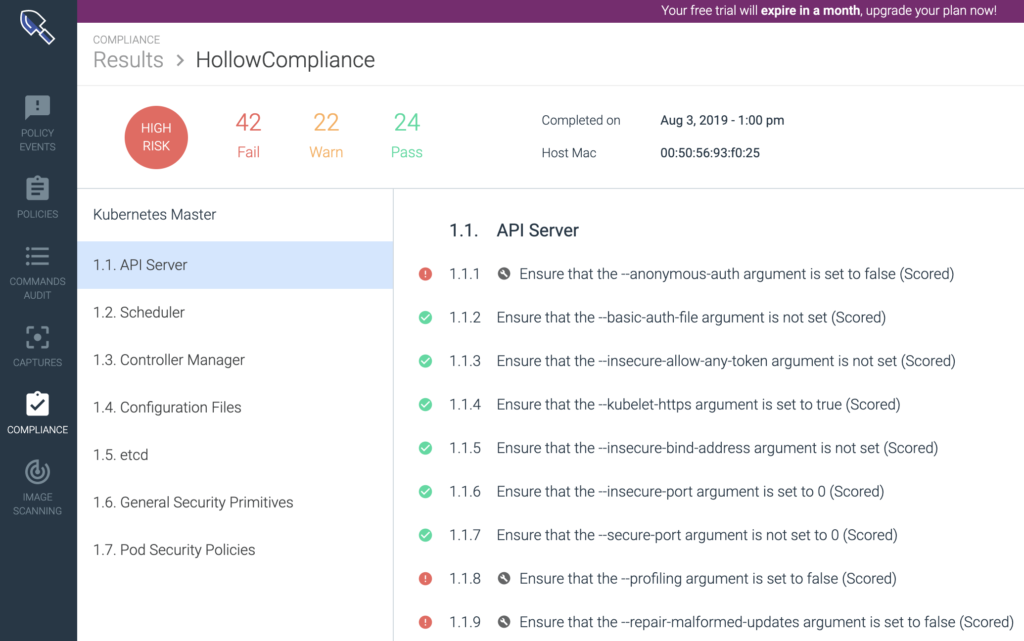
Secure Compliance
If you need to baseline your environment with some standard compliance frameworks like the Center for Internet Security (CIS) then the compliance piece of Sysdig Secure will get you started. Here you can quickly view if you’ve deviated from the industry best practices. Users are also given data as metrics so each compliance run is a full audit trail. You can see my k8s API server compliance. Failures in my lab were created for illustrative purposes only of course :)
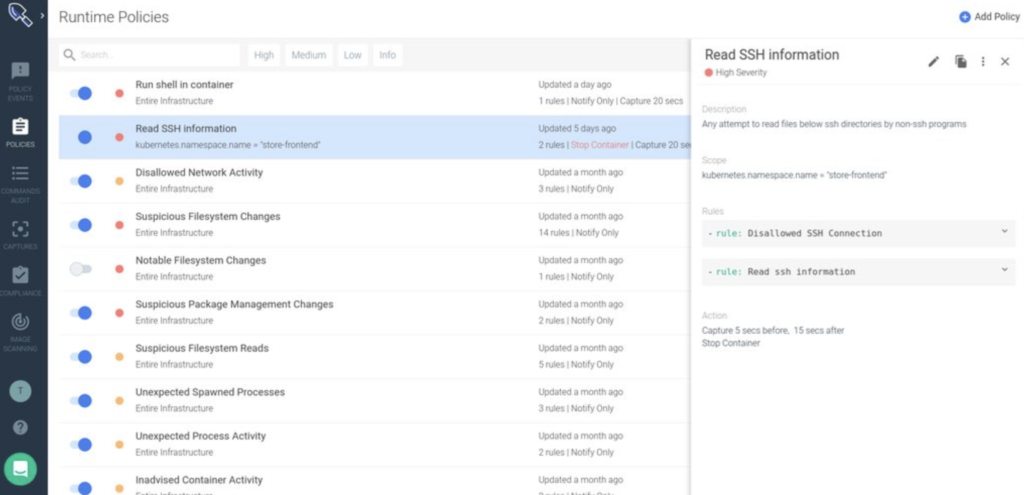
Secure Runtime Security
We’ve got to constantly be reviewing our environment for changes to ensure that our hardened environment hasn’t been weakened along the way. The Runtime security from Sysdig keeps us appraised of changes to our environment like the addition of a privileged clusterrole for example.
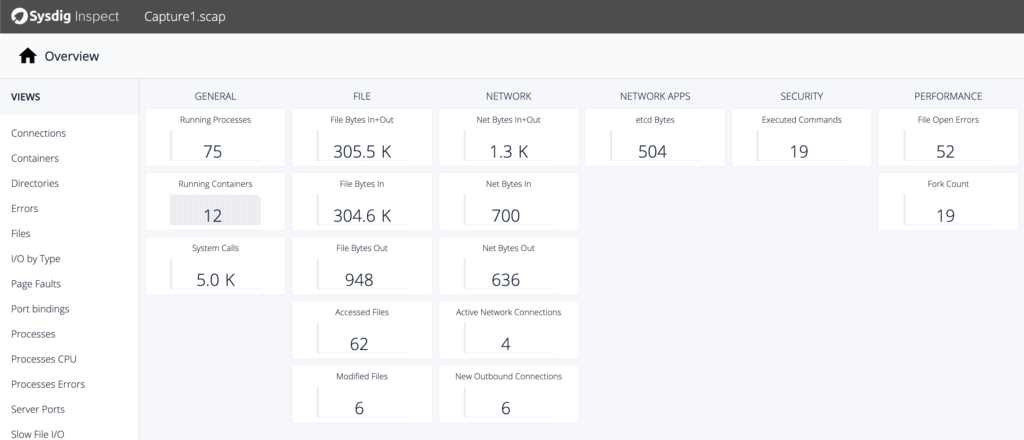
Secure Forensics
Despite our best efforts, sometimes we still have issues in the environment that need investigated. Or, hopefully, we just need to do some investigation for an audit to prove that we really are highly secured. Sysdig Secure provides the ability to capture whats happening and dive into the details over defined period.
Summary
If you’re not sure how you’re going to protect your Kubernetes environment, maybe go have a discussion with a Sysdig representative or partner to see what can be done to get you started in your journey. Good luck!