In part 1 of the series we covered some generalities about Microsoft Dynamic Access Control and a few steps needed to prepare the domain and file servers. Now let’s look at creating claims.
A claim is a user, device or resource property. A user in Active Directory will have properties such as Location, Department, manager, etc. Each of these properties is a claim but for any actions to be utilized by Direct Access, they have to be defined.
The example that I use below is creating a claim and then using that claim to assign permissions to a folder.
Create a User Claim
Setting up claims is done from the Active Directory Administrative Center (ADAC). Click the Dynamic Access Control (DAC) tile and you’ll notice a series of steps. Create a claim type is the first step. Click the hyperlink and you’ll be taken to the correct window, or use the Dynamic Access Control link on the menu and choose claim type.
This example uses the Active Directory property “department”. In the list of attributes typing in department will help to filter the available properties. Give the claim type a name, such as “department”, on the right side, and select what kind of claim it will be. In our case this is a “User” claim.
NOTE: Device claims require Windows 8 devices (or higher) to work properly.
At the bottom of this window, add some suggested values. For Example in my lab, there are a few departments including IT, Communications, Human Resources, etc.
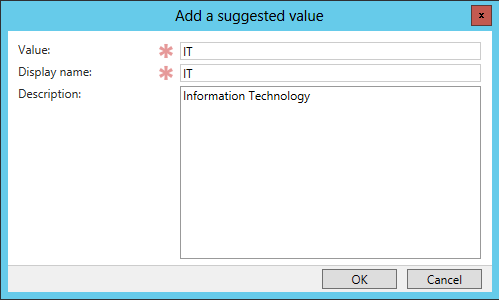
Add a claim’s suggested Values
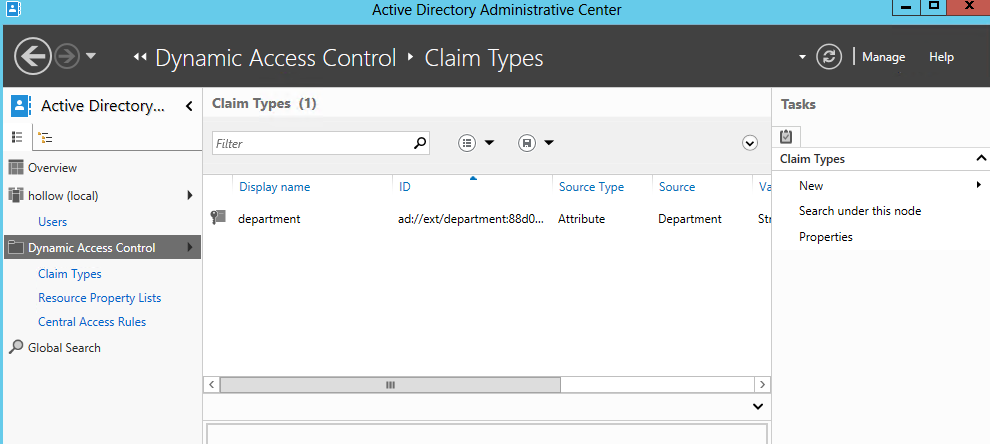
When the claim has been added, the ADAC will show a display name, ID, Source Type, etc as a claim. Multiple claims can be created at any time, or modified.
Securing a folder by Using a Claim
Now that we have a claim created, lets modify the security of a folder to allow access to anyone in the IT Department.
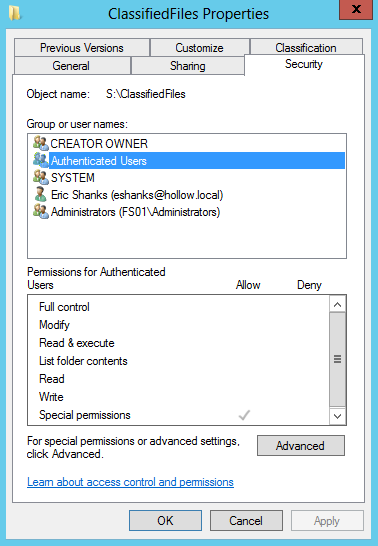
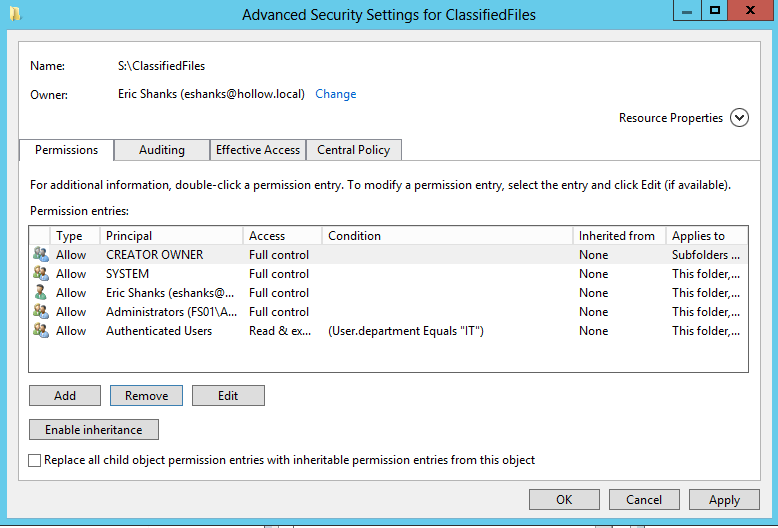
My folder security on “ClassifiedFiles” looks like the below screenshot. Notice that “Authenticated Users” does not have read permissions on the folder.
To allow access to anyone in the IT department we’ll select the Advanced button.
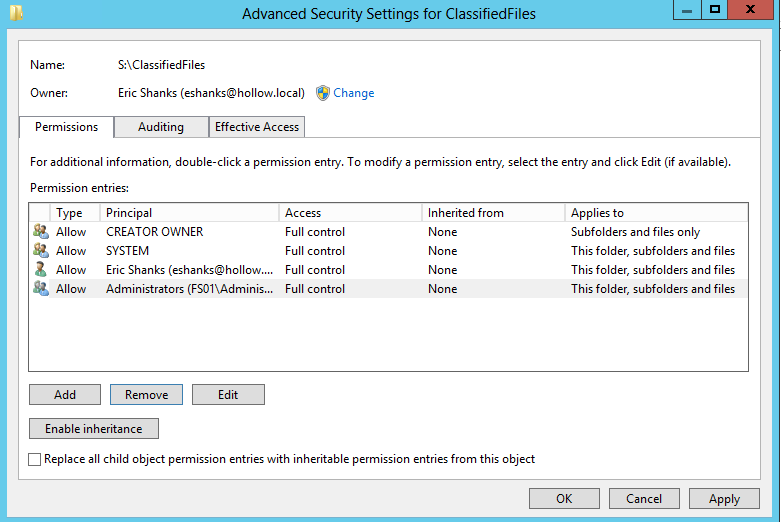
Here in the Advanced Security Settings, we can add a new permission entry.
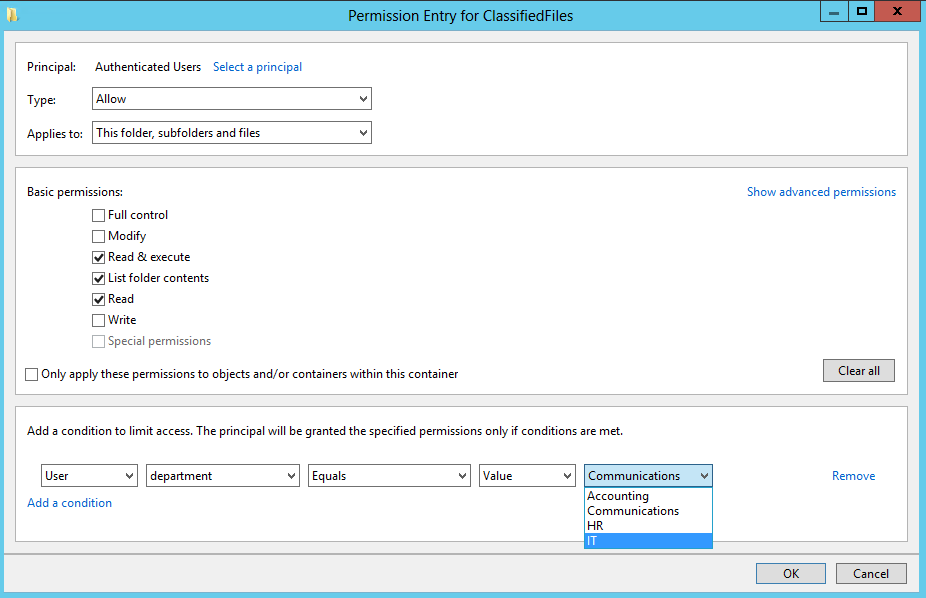
Click the link to add a principal. In our case we added “Authenticated Users”. This will mean that any users that are authenticated to the domain and are in the IT Department will have access.
Change the type to “Allow” and set the permission. I’ve added Read and Execute permissions.
The part of this screen that deals with the claim we setup earlier is listed at the bottom. Click the “Add a condition” link to add our claim. Here we’ve added the information for the User Claim, department, and which value we want to grant access. Here I’ve added IT.
NOTE: It is possible to add multiple conditions to limit user access. If you have two claims and want both of them to be true, you can add a second condition with an ‘AND’ operator. An example might be only allowing the IT department in the Chicago Office to access these file, but limit access to the IT department in San Francisco.
When you’re done an additional permission entry will be added to the advanced security settings for the folder. Shown below.
Testing Access
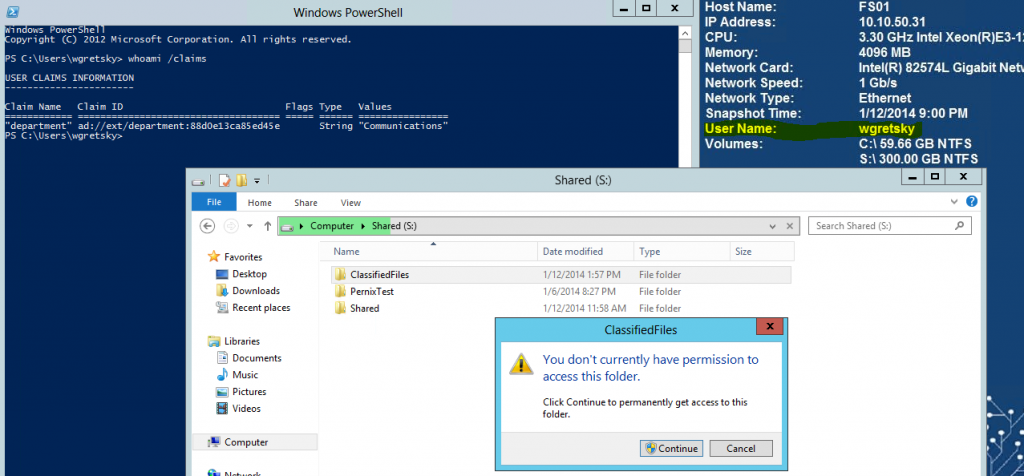
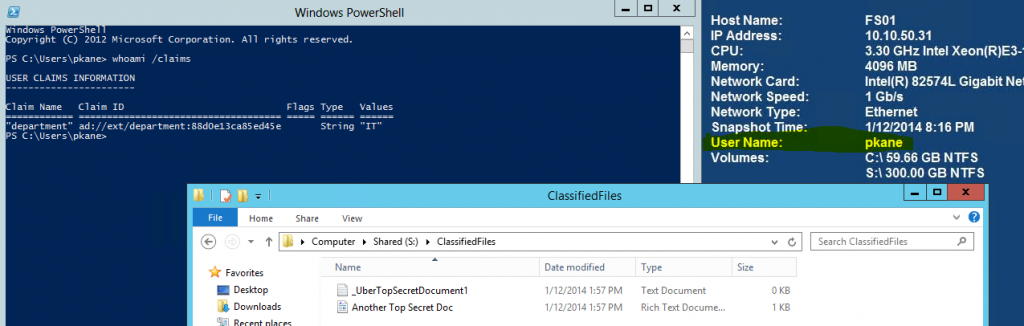
If it hasn’t been tested, it doesn’t work. So here is my test. I used two employees, one in the IT department and the other not in the IT department and tried to access my classified folder.
When I log as Mr. Gretzky, he does not have access to the folder and receives an access denied message. We can also verify this user’s claims by utilizing the whoami /claims command form a powershell window. I’ve included this in the screenshot to prove out our example.
I then login as Mr. Kane (Go Hawks!!!) and have access to the folder as expected.
 Claims are an important thing to know for securing files going forward because they can significantly reduce the number of groups needed to be created.
Claims are an important thing to know for securing files going forward because they can significantly reduce the number of groups needed to be created.
In future posts, we’ll see how Resource Properties can also be added to further reduce manual tasks.
Dynamic Access Control Series Initial Configuration Steps for Microsoft Dynamic Access Control- Part 1 Claims – Part 2 Resource Properties – Part 3 Access Rules and Policies Part 4 File Server Resource Manager Auto Classification - Part 5