So far we’ve covered:
In this post we’ll look at Resource Properties.
Resource Properties
A resource property is a claim that describes the characteristics of an object in the file system. A claim is a descriptor of a user or a device whereas a resource property is a characteristic of a file or folder.
As an example, we have a folder with HIPPA related information in it. A description can be added to this folder to indicate that it has Protected Health Information (PHI) contained in that folder. This PHI description is a resource property.
Enable and Create Resource Properties
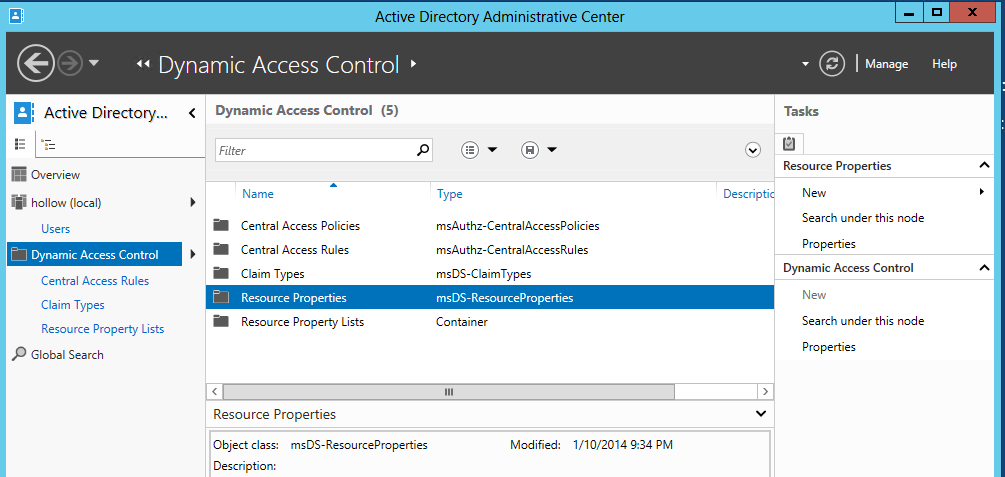
There are lots of properties that Windows has available to use right out of the box on a File Server with FSRM installed, but they aren’t available to be used immediately. They have to be enabled first. To do so, we go back into the Active Directory Administration Center (ADAC) and go to the resource properties settings for dynamic access control.
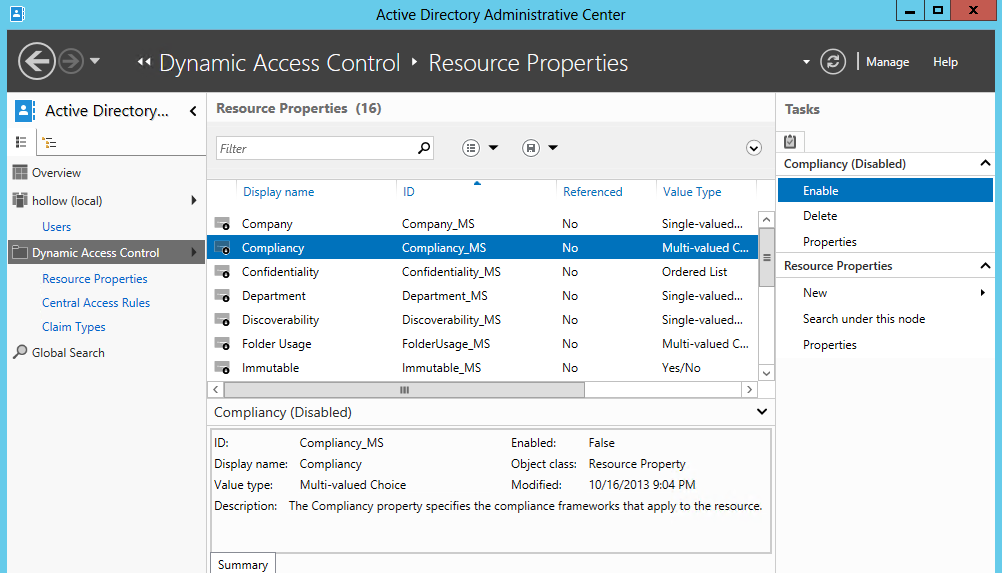
Here you’ll see that there are plenty of properties already available. Select the properties you’d like to use and click “Enable”. In the example below, I’ve chosen to use “Compliancy” for no specific reason.
You may also find that your organization has different requirements for resources and wants to add some custom properties. No problem there, just click the New link on the right side and add your own properties.
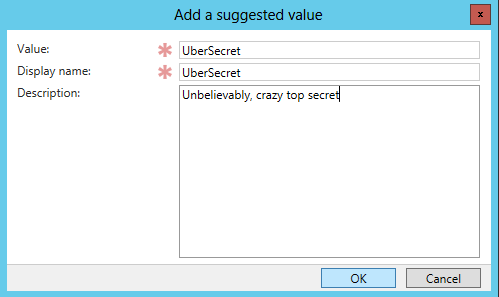
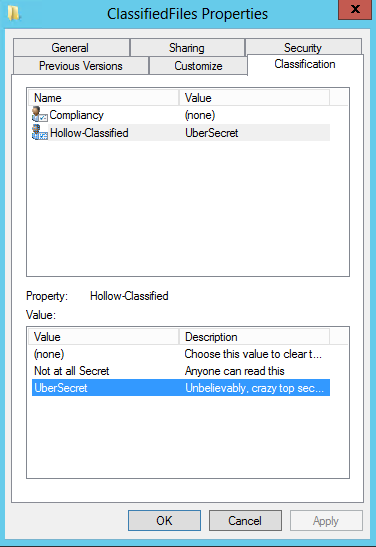
Here I’ve created a rule called “Hollow-Classified” and made it a single-valued Choice. 
I added two suggested values of NotSecret and UberSecret.
Add Resource Properties to FoldersFiles
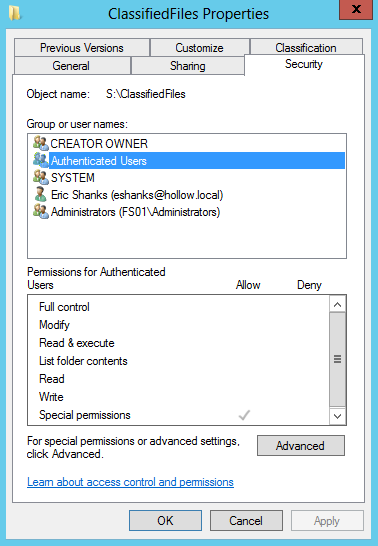
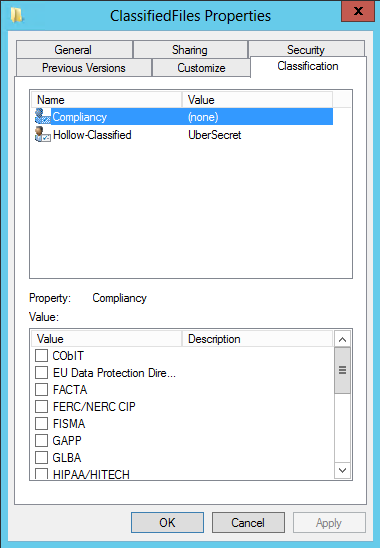
Now we need to go to our folder that we’re going to add a property on. Open the properties of the select folder and look for the Classification tab. Here you will see the resource properties that are enabled, and you can assign them a value based on the characteristics of the folder.
In the below example, I’ve left the “Compliancy” property blank but changed the “Hollow-Classified” property to “UberSecret”. You may set multiple properties for the same folder.
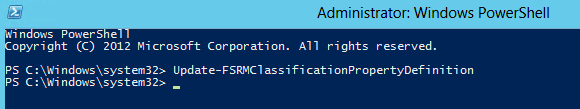
NOTE: If you open the folder properties and the characteristic tab is empty, either wait for the classifications to update, or run the powershell code below to force this update to happen.
Update-FSRMClassificationPropertyDefinition
Assign Permissions using Resource Properties
Now that a folder has a property on it, we can use those properties to assign permissions.
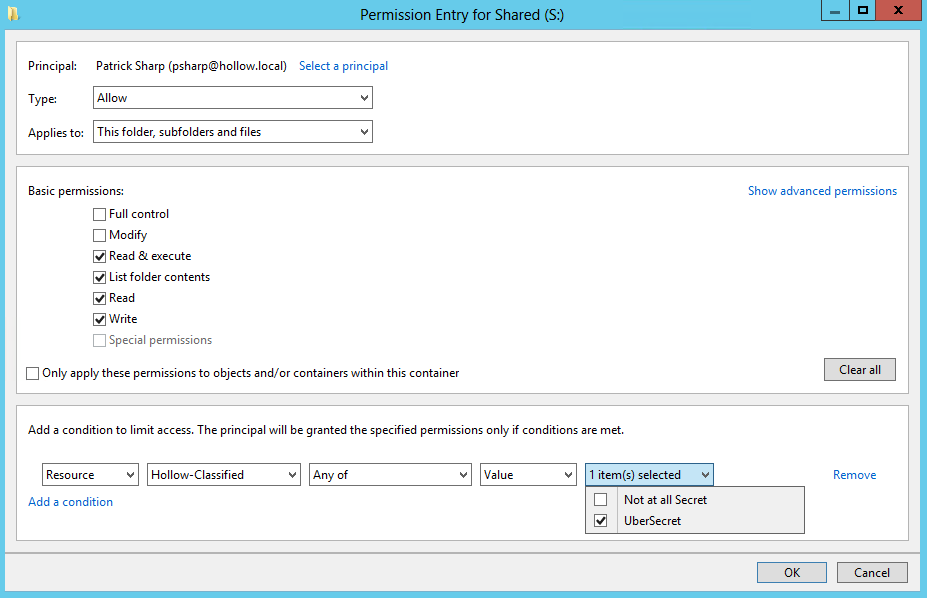
Similarly to how we added claims permissions to a folder, we open the Advanced Properties of the security tab of the folder.
My test user is named “Patrick Sharp” so I’ve selected him as the principal, granted him the Read and Execute permissions on the folder and then added a condition to the bottom of the entry. I chose Resource, selected the “Hollow-Classified” property where the value was “UberSecret”.
This means that anytime Patrick Sharp tries to access a file in this folder that has the UberSecret Classification he will be allowed access (assuming there isn’t another Deny permission added on the filefolder negating this configuration).
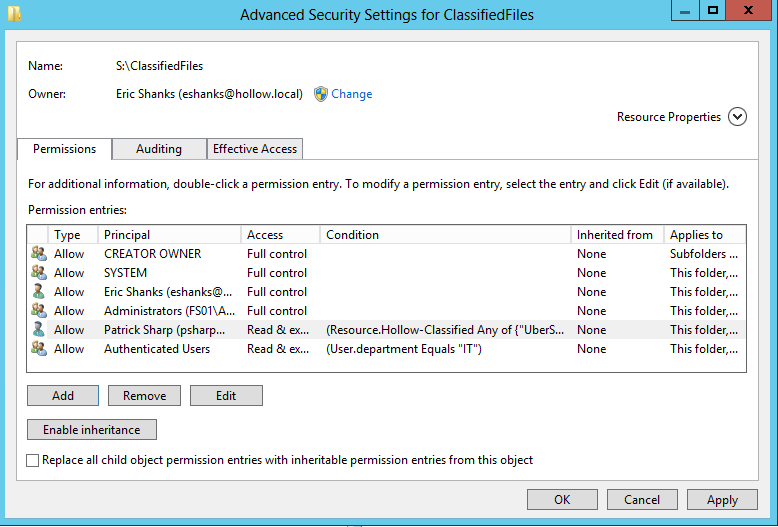
Once the setting is added, the permissions will reflect the new access.
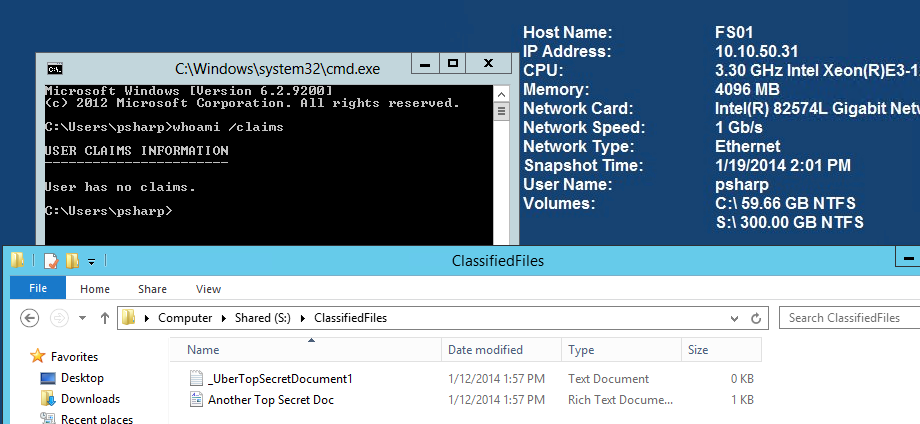
Lastly, I log in as Patrick Sharp and test the permissions. I find that I do have access to this folder as long as it’s classified as “UberSecret”.
Summary
Resource Properties are much like user or device claims, except they are used on a file or folder. These might not seem incredibly useful to you yet, but we’ll see in future posts that claims and resource properties can be combined to be very powerful in managing document security.
Dynamic Access Control Series Initial Configuration Steps for Microsoft Dynamic Access Control- Part 1 Claims – Part 2 Resource Properties – Part 3 Access Rules and Policies Part 4 File Server Resource Manager Auto Classification - Part 5