It may be necessary to connect to a Linux Guest thats that been provisioned in Amazon Web Services so that you can perform additional operations on it. One of the ways you might want to configure your instances is through vRealize Orchestrator. One of the hang ups with using vRealize Orchestrator to connect to your Linux EC2 instances is that you’ll need an SSH key to connect. This post shows you how you can do this.
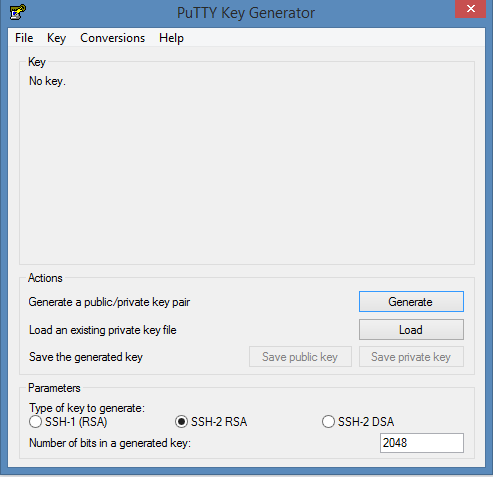
First, go get the SSH certificate used when creating the virtual machine. This should come as a .pem file from Amazon EC2 and you’ll only have one chance to download it. This key will allow access to the guest OS so it will be needed. Next you’ll need to convert that certificate to a .ppk file. To do this we’ll use a program called puttygen. Run the executable and click the “Load” button to load the existing private key.
Next, click the save private key button to save that key. Name it the same name as the original .pem file, but change the extension to .ppk. At this point if you want to test the key, you can load it into putty and connect to the instance to try it out. 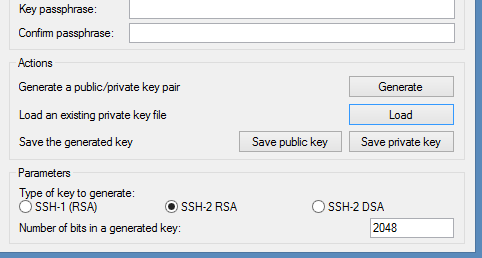
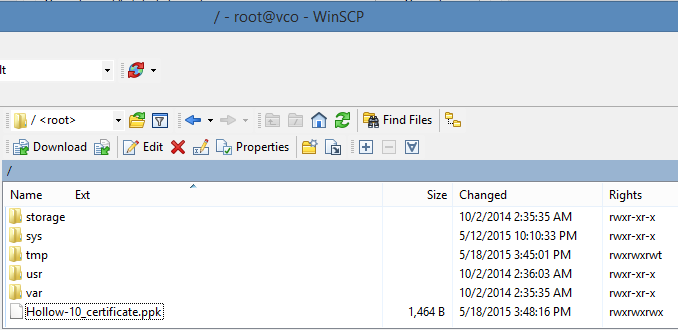
If we want to use vRealize Orchestrator (vRO) to connect to this instance later on, we can save the .ppk file on the vRO appliance. I used WinSCP to copy the file from my Windows machine, over to the vRO server.
Once the .ppk file is copied over, make sure that the vRO Server has permissions to read the file. I set read permissions on the file after copying it over. 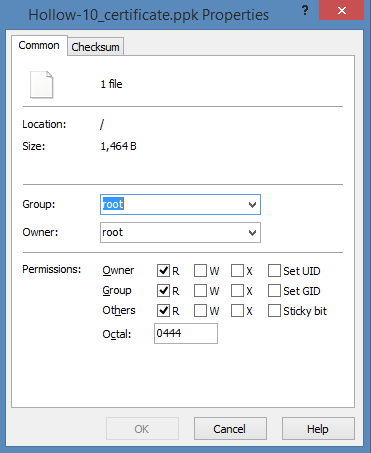 Sidebar - OK, I know what you’re thinking. If I plan to use vRO to connect to this instance later, that means I’m doing some automation in my environment. So far, all of the steps that I’ve outlined are pretty manual steps and not useful. While this might be true, if you’re using a product like vRealize Automation (vRA) you can set a key pair per reservation. So if you use the same key on a reservation, all of the machines provisioned on it will use the same key. This means you only need to add a key to the vRO server for each reservation.
Sidebar - OK, I know what you’re thinking. If I plan to use vRO to connect to this instance later, that means I’m doing some automation in my environment. So far, all of the steps that I’ve outlined are pretty manual steps and not useful. While this might be true, if you’re using a product like vRealize Automation (vRA) you can set a key pair per reservation. So if you use the same key on a reservation, all of the machines provisioned on it will use the same key. This means you only need to add a key to the vRO server for each reservation.
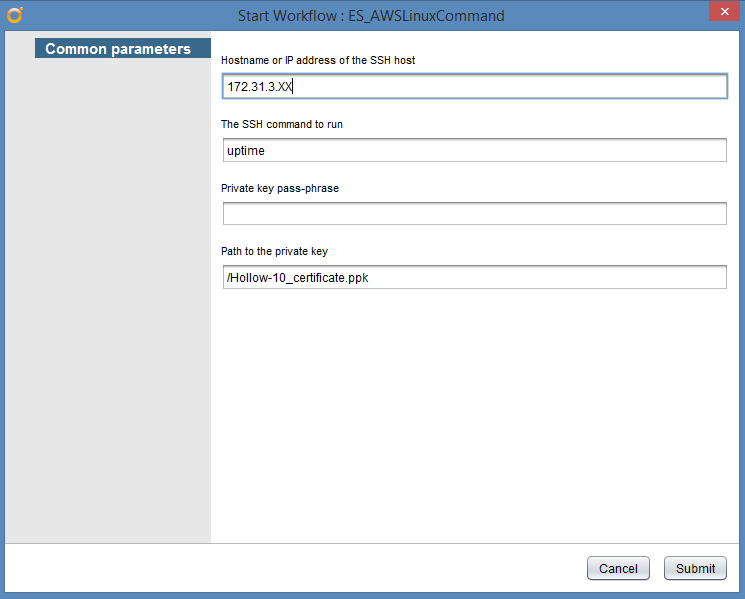
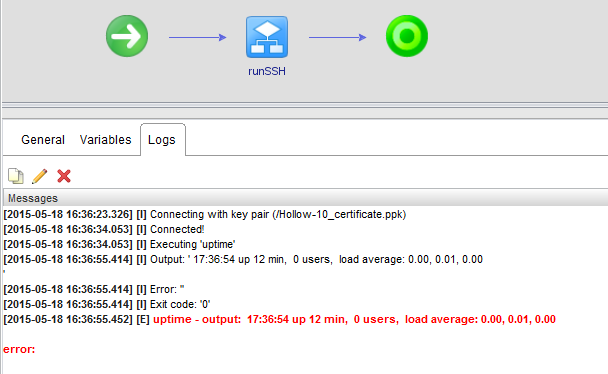
Now we can create a workflow in vRealize Orchestrator to use the “Run SSH Command” workflow. I’ve used a slightly modified version of that workflow to connect to one of my instances in EC2. The main things to add though, are the Hostname or IP Address of the EC2 Instnace, the SSH Command to run and the location to the private key which is in the / directory.
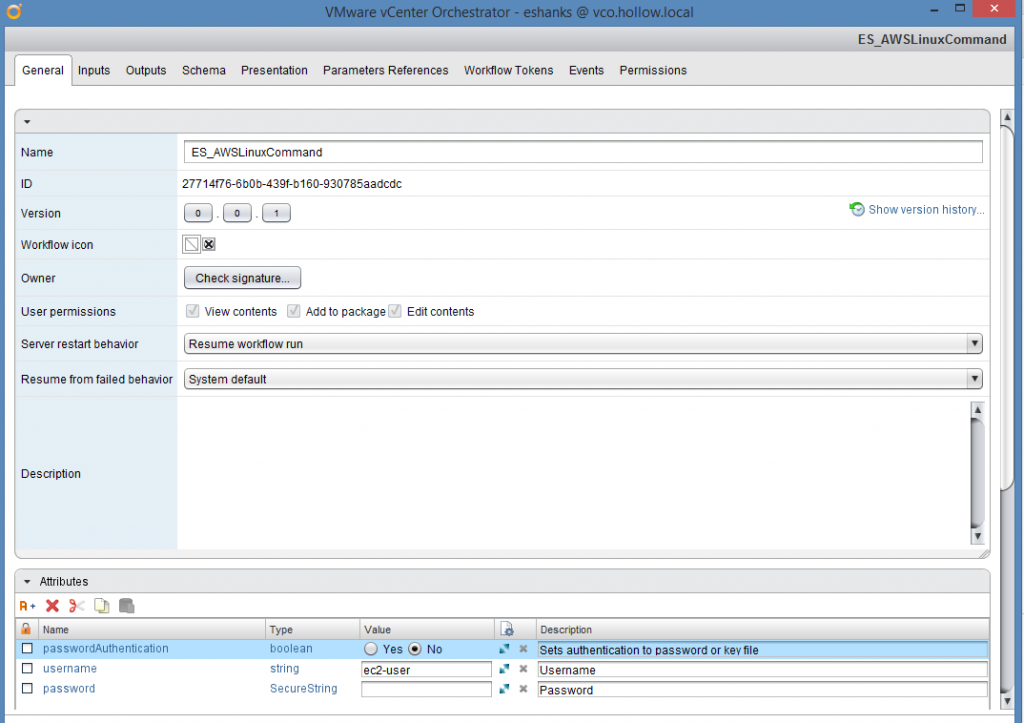
Notice also that for my modified workflow, I’ve added the username “ec2-user” as an attribute as I know it won’t change between runs.
When I run the command, you can see the output in the logs.
Summary
Running SSH commands on your EC2 instances might not sound all that fun, but since there is not VMware Tools installed on the machine, its a little more difficult to access the guest OS to install programs or make configuration changes. At least by using this method, we can reliably access the guest OS from Orchestrator.