If you’re an Amazon Web Services customer and you’re not using the built in AWS config rules, you should be. AWS Config is a service that shows you the configuration changes that have happened on your AWS accounts. Whether that’s changes to your user accounts, changes to networks, modifications to S3 buckets or plenty of other configurations. AWS Config will keep this audit log of your changes in a specified S3 bucket which could be used for all sorts of other solutions such as updating your ServiceNow configuration management database. See this post from ServiceNow on some details of the solution.
OK, well maybe going that far is too much for you to begin with, but AWS Config also provides some very useful and basic rules that can alert you when something in the environment isn’t the way you want it. Amazon has provided some of the most common best practices checks to help you get started.
Add AWS Managed Config Rules
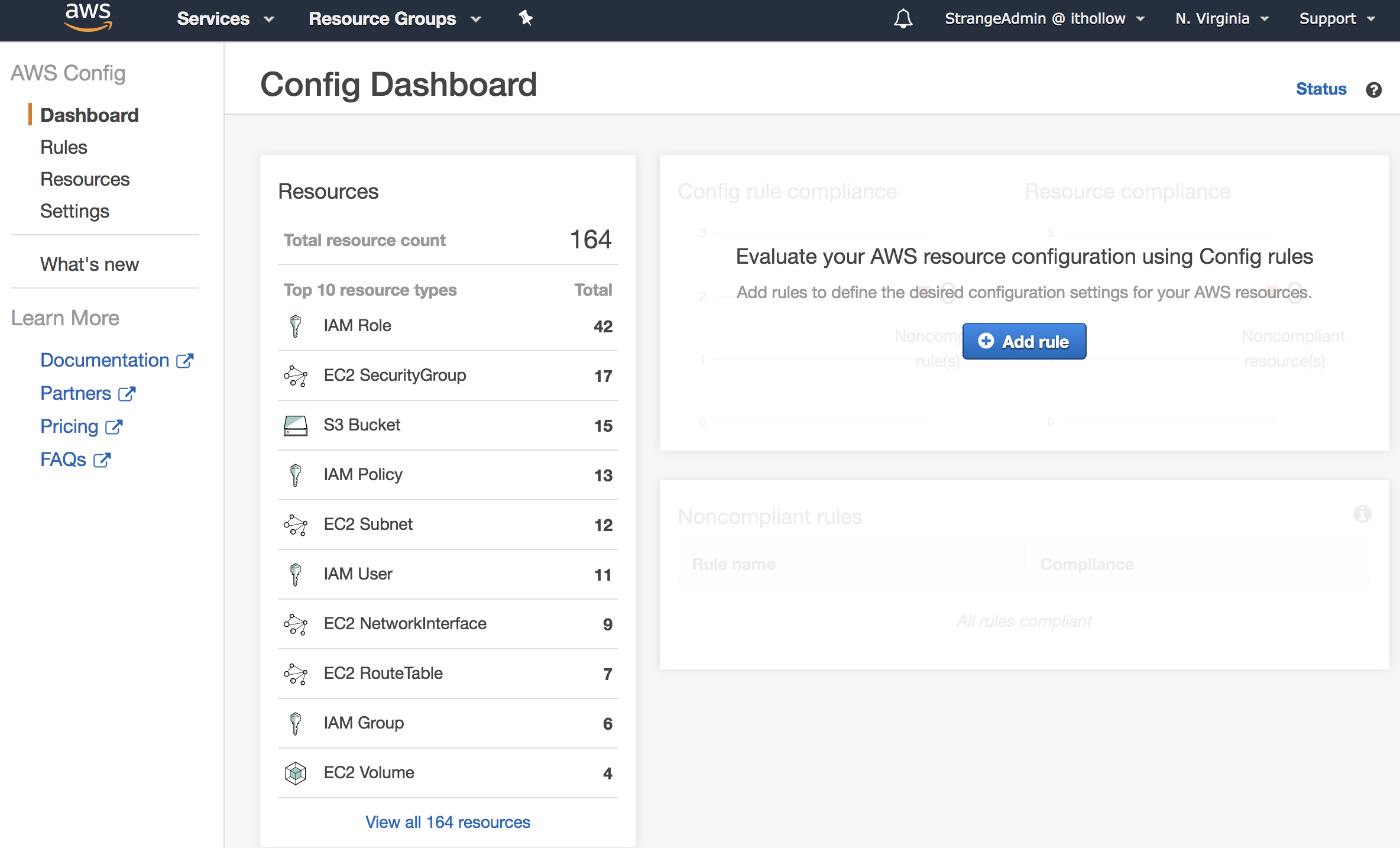
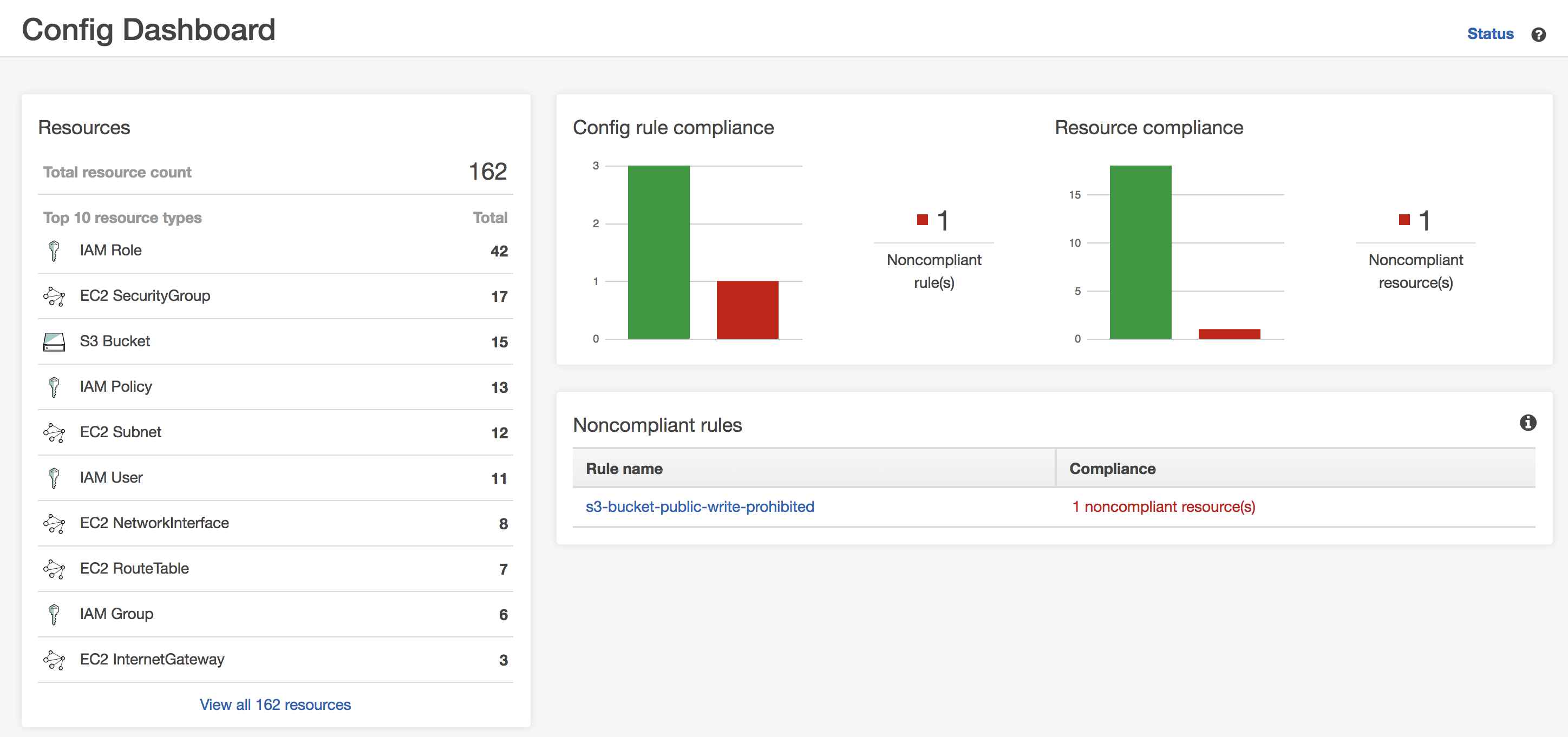
Login to your AWS Console and go to the AWS Config service. Click the Dashboard and we’ll see some information about some of the services in your account. On the right hand side you’ll see the “Add rule” button unless you’ve set some up in the past, in which you can then click Rules in the menu to get to the same screen. Click the “Add rule” button.
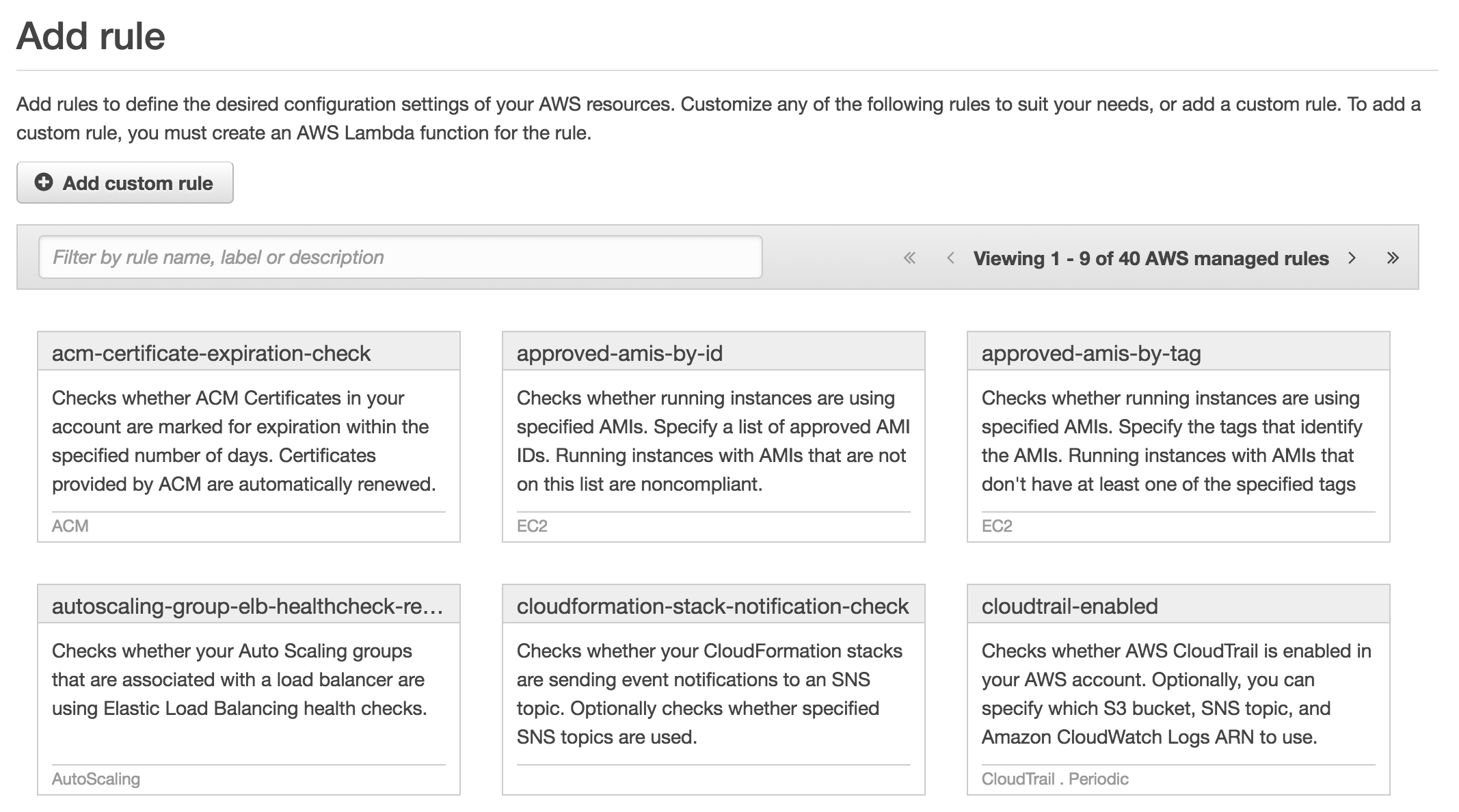
On the Add rule screen, browse through the list of managed rules that AWS has provided for us. When you see a rule that you’d like to use select it from the list.
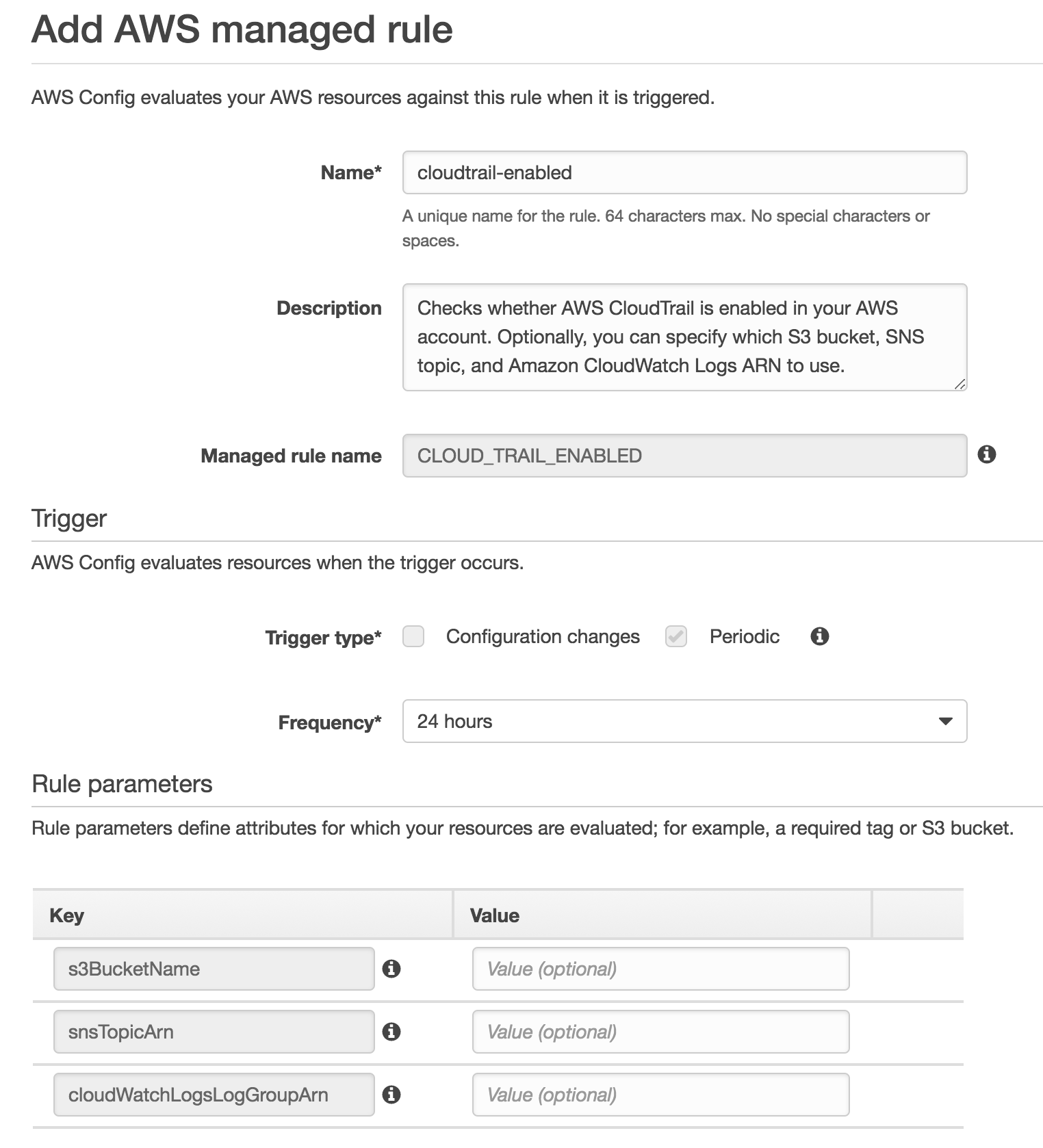
The first rule that I’ve chosen to add is the CloudTrail-enabled rule. CloudTrail is a service used to audit all API and Console changes so that we can go back at any time and see what’s happened to our account. As a best practice it should always be enabled and I want to make sure that this is the case with my account. So once we add the rule, we’ll need to enter in some information for the rule to be used successfully. Depending on the rule that you’ve selected, the information needed to configure it will be different. In my case I need to add a frequency for the rule to run, which could either be a schedule, or on a configuration change. Since this is a lab account, a schedule will work for me. After that I need to enter in some optional information about my CloudTrail configuration.
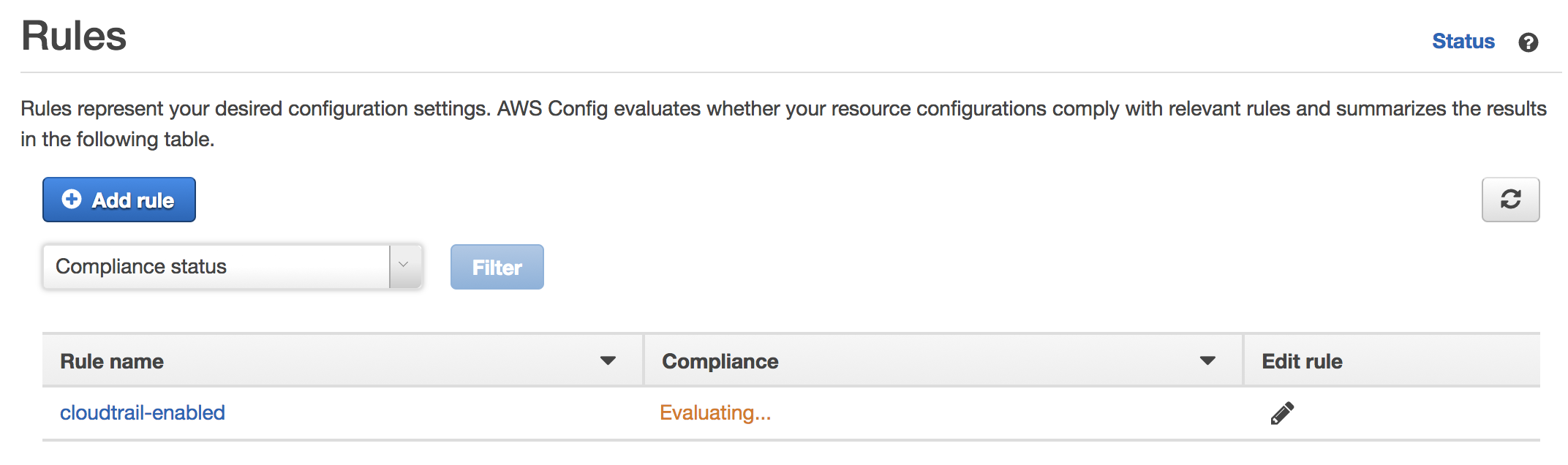
Once you’re done modifying, click save to add the rule. The rules screen will show up with a list of your rules and will show Evaluating until the checks are all done.
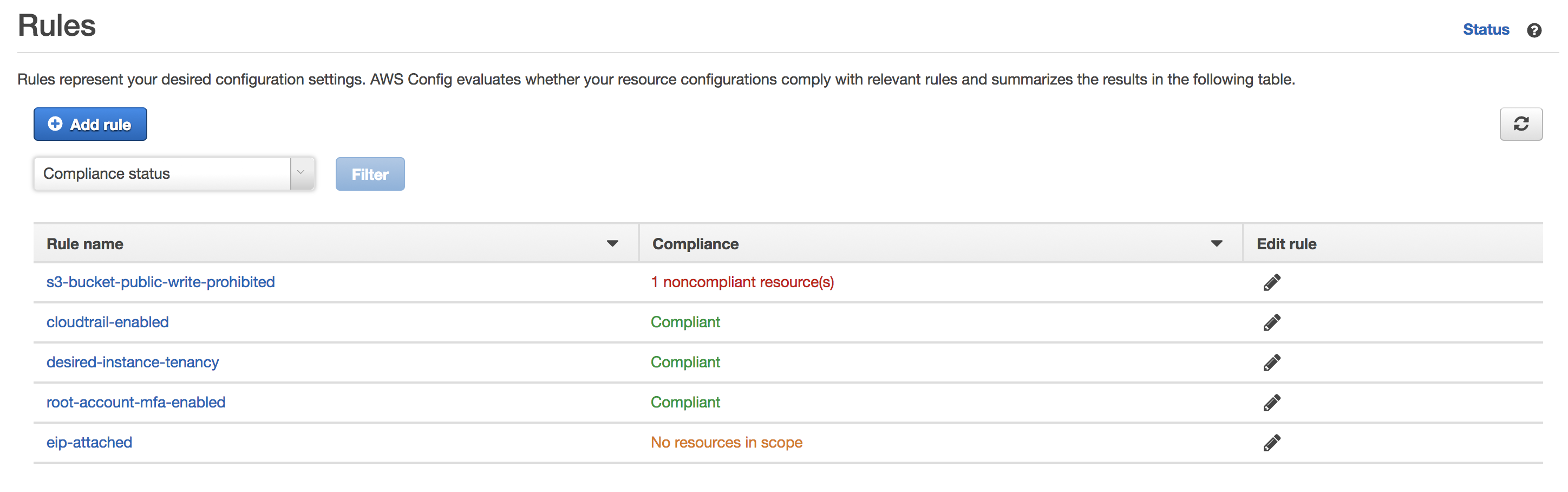
At this point, feel free to add any other rules that you might find useful to protect your account from unwanted changes such as publicly accessible S3 buckets, Security Groups that are open to the Internet and a whole list of others that require almost no work on your part to get setup. As you can see from my list, I have a writeable S3 bucket that is publicly accessible. Probably not a good thing in many cases, but in my case it’s just fine. In my lab, I’m also making sure that root accounts have multi-factor authentication enabled and my tenancy model is shared.
Rules Dashboard
Once you’ve setup all your rules and they’ve had a chance to go through your account to evaluate the settings, you’ll have a nice dashboard with some basic information about your account. This allows you to check some very basic settings at a glance.