Multi-Factor Authentication or MFA, is a common security precaution used to prevent someone from gaining access to an account even if an attacker has your username and password. With MFA you must also have a device that generates a time based one time password (TOTP) in addition to the standard username/password combination. The extra time it might take to login is well worth the advantages that MFA provides. Having your AWS account hijacked could be a real headache.
Setting up MFA
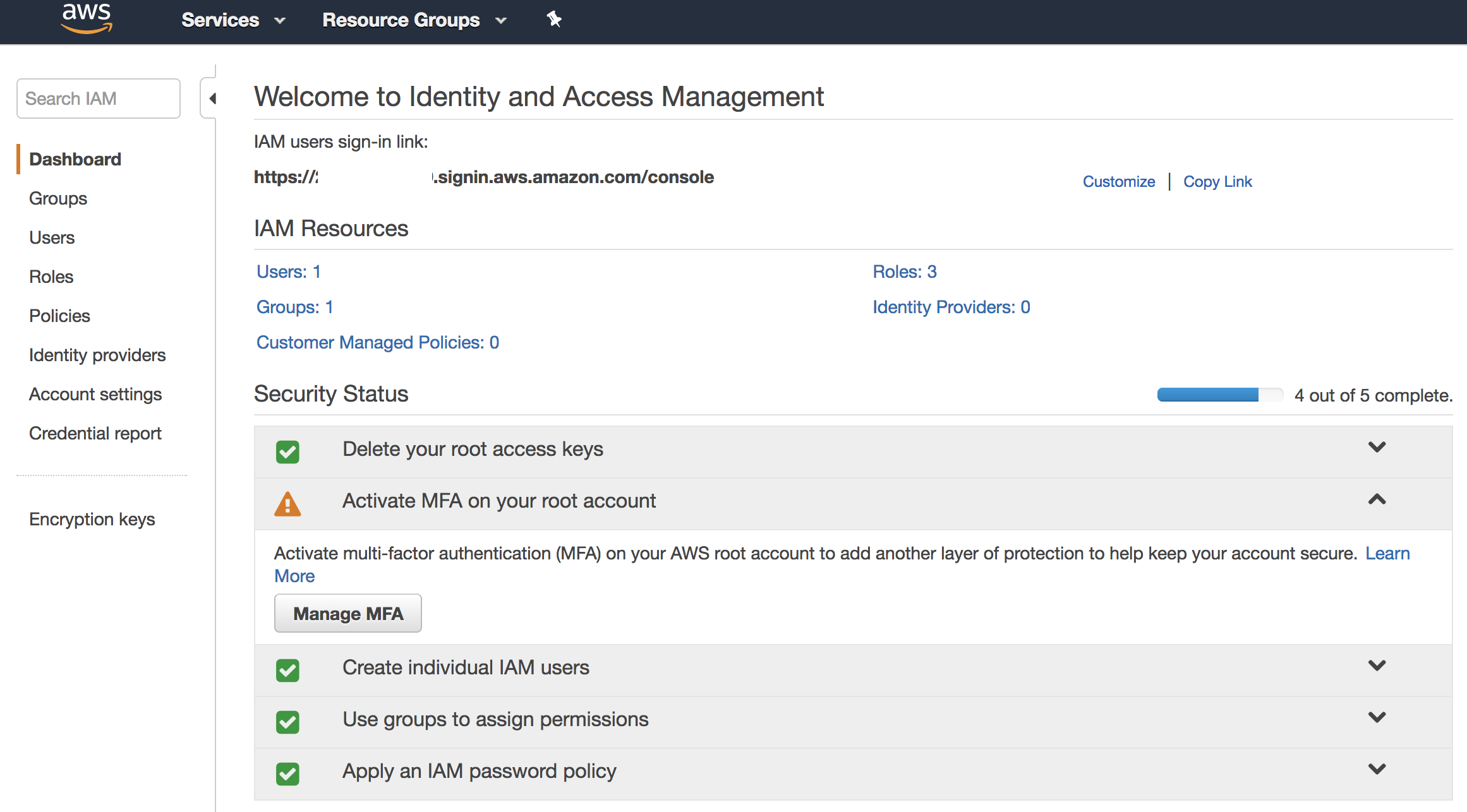
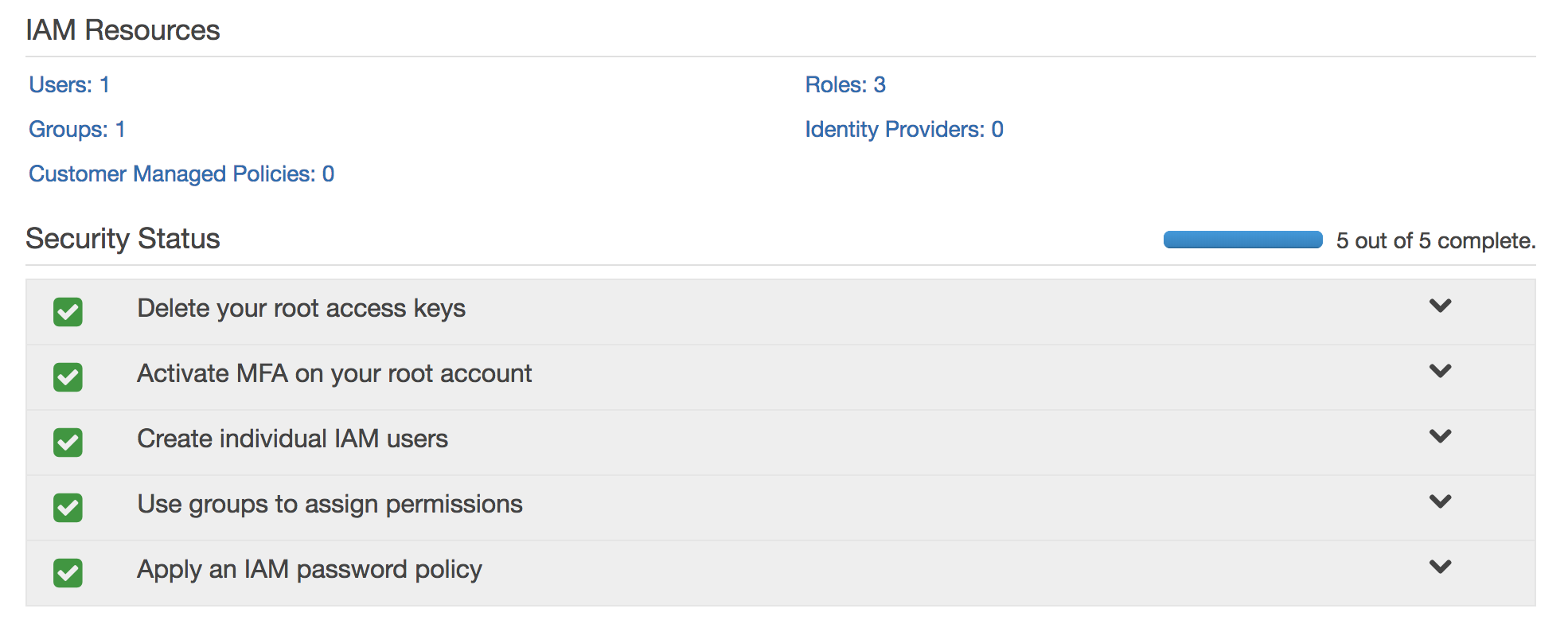
Setting it up is pretty easy. First login to your AWS account. I’m security my root user account so I’m going to the IAM console and looking at the dashboard. As you can see I have a very unsightly orange/yellow exclamation mark in my security status dashboard. If you’re like me, we can’t have any of those hanging around. Click the dropdown and then select the “Manage MFA” button.
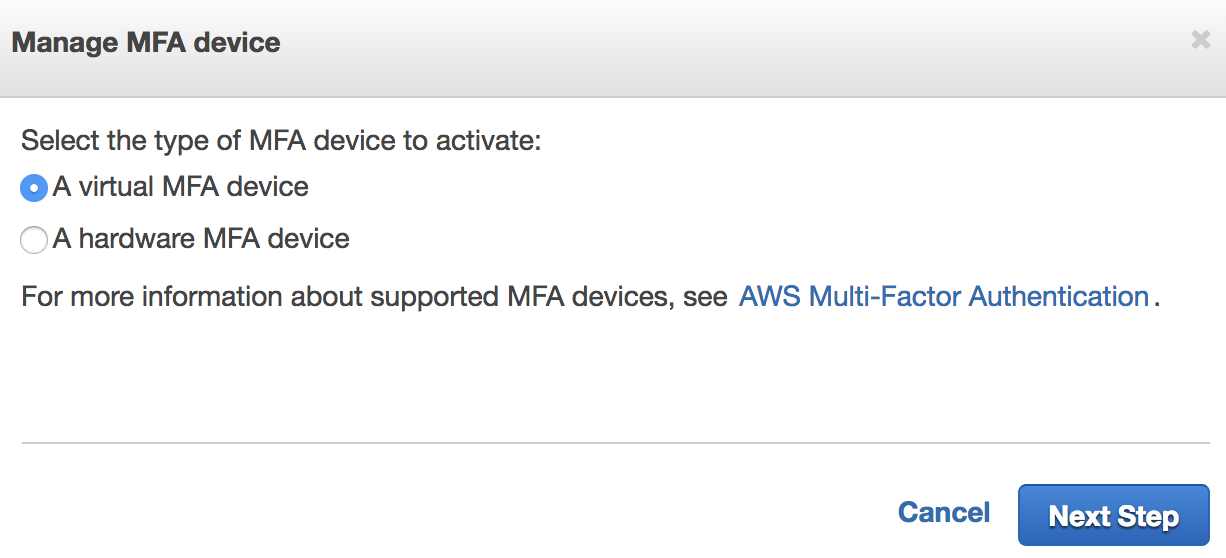
A dialogue window will pop up asking what kind of device to use. I’m using my smartphone which isn’t quite as secure as a hardware MFA device, but still pretty good. Click the “Next Step” button.
The next screen is just letting you know that you’ll need to install an AWS MFA compatible application on your phone. I’m using OKTA Verify which works fine, but there are others you can download such as Google Authenticator or Authy. For more information on this see: https://aws.amazon.com/iam/details/mfa/.
Once you’ve installed an MFA app on your phone click the “Next Step” button.
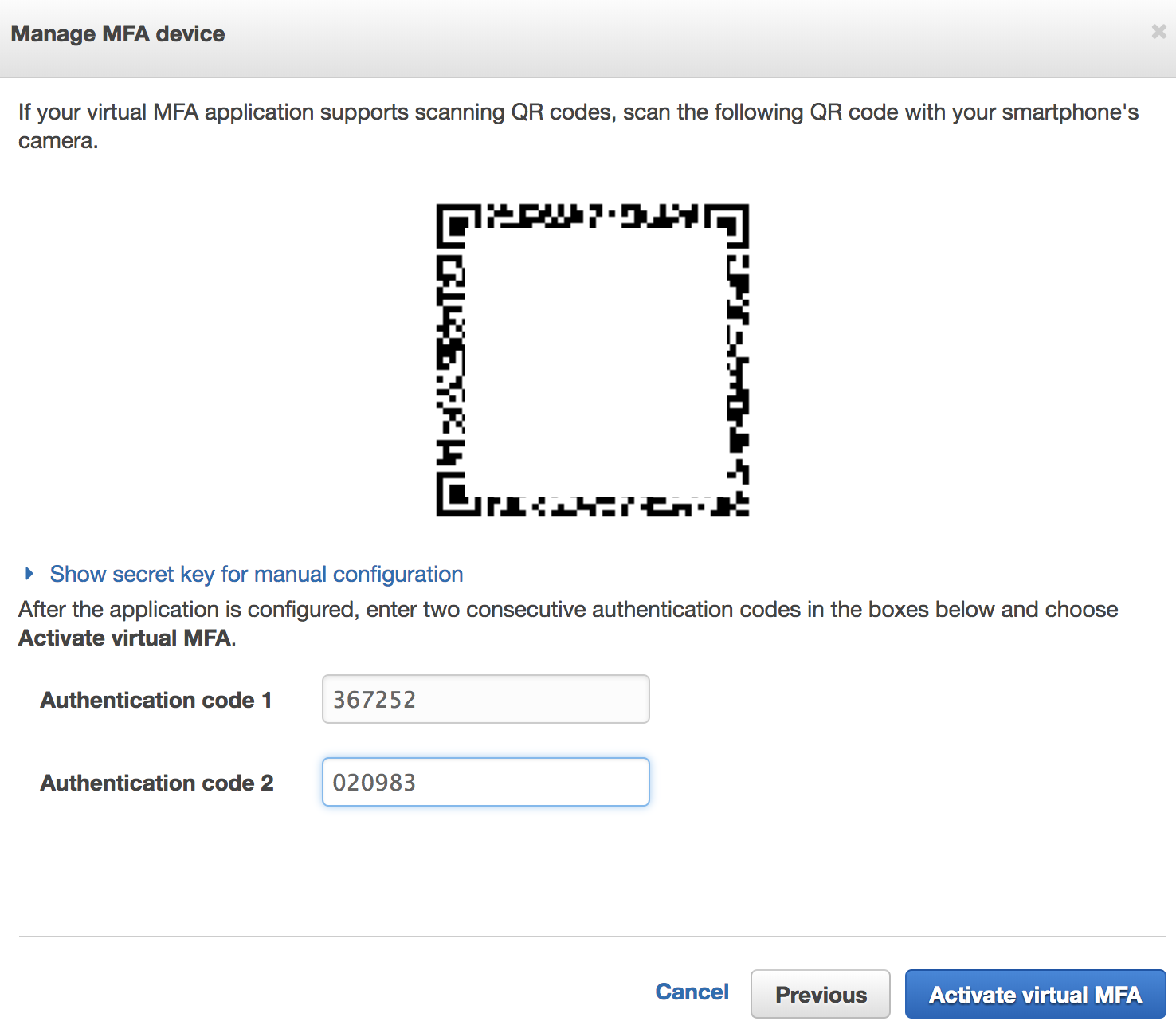
On the next screen you’ll be given a QR code to scan with your MFA application that was just installed on your device. Scan the QR code that pops up on the screen. After this, you’ll need to put in the next two codes that your MFA app provides so that it sync’s with AWS. When you’re done with this step, click the “Activate Virtual MFA” button.
NOTE: You should screenshot the QR code and store it in a SAFE PLACE! If you lose your phone or something or need to reset your MFA, you’ll need to re-scan this QR code. You can’t retrieve this QR code again from the AWS console so it’s up to you to store it in a safe place. I store mine within my 1Password vault along with my AWS credentials.
If all went well you’ll get a success message.
If we look at the IAM dashboard again, we’ll see our green checkmarks and we’re good to go.
“If the light is green, the trap is clean” -Ray Stanz
Result
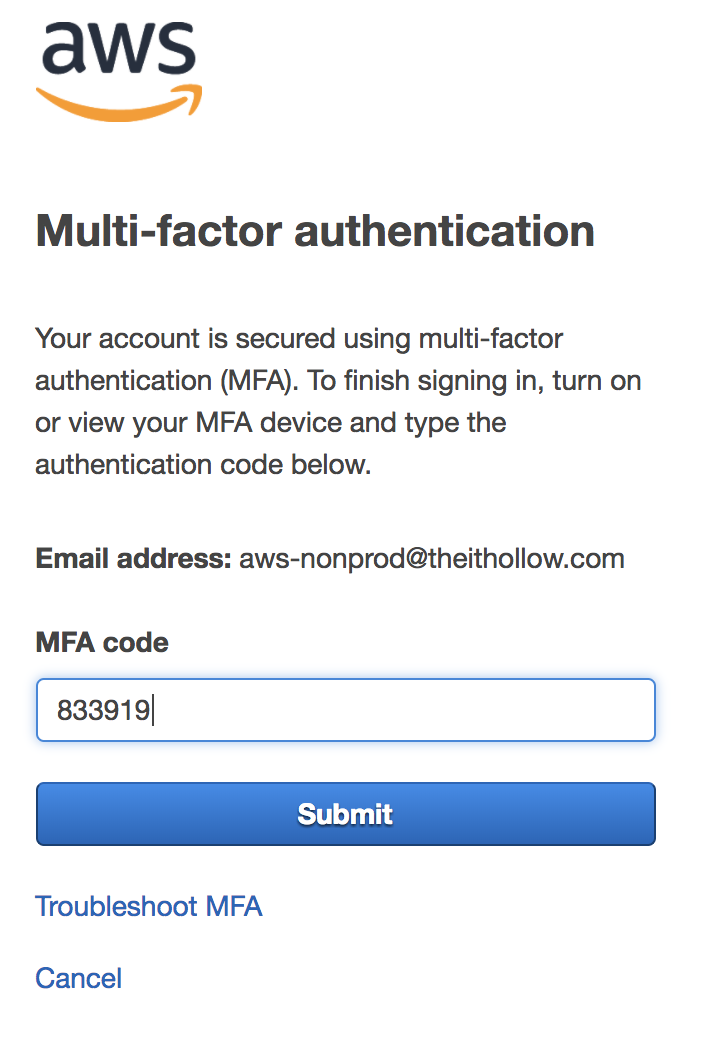
When we go to login to the AWS account the next time, we’ll be prompted to enter in a one time password after entering the username and password.