Zoning and Lun Masking are often confused for each other, probably because both of them are used to restrict access to storage. They should both be used to secure the storage network and reduce unnecessary traffic.
Zoning
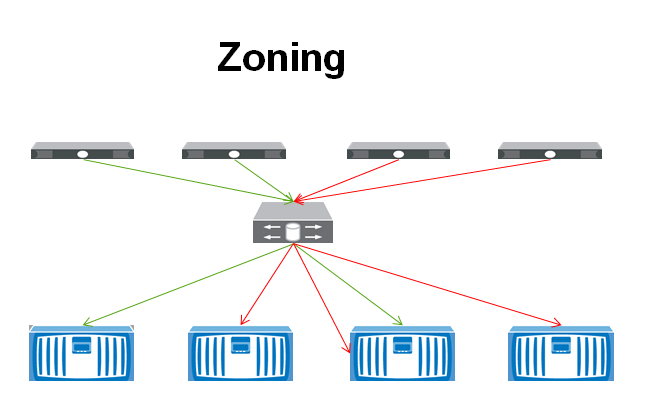
If you want to specify only certain hosts from accessing a storage device then you would want to setup zoning. For instance, in the example below, you can see that the two servers on the right can access three of the four storage devices, whereas the two on the left can only access two of the SANs. This configuration is done on the Fibre Channel switch. iSCSI, NFS, and FCoE can also be segmented, but they would use typical TCPIP segmentation methods like setting up a VLAN.
There are two type of zoning techniques: Hard Zoning and Soft Zoning.
Soft zoning filters one device from seeing another device. However, if the ports are manually setup, the switch will not stop the devices from communicating. Hard zoning by comparison prevents one port from sending traffic to the other port and is more secure.
Zoning can also be setup based off the port or the World Wide Name (WWN). Port zoning grants access from one port on a switch to another port on a switch. This would require physical security to be setup around the Fibre Switch, because the zones could be changed around simply by moving the cables in the switch. This also makes it more of a struggle for management if switches need to be moved or re-cabled. WWN zoning is setup by allowing access between two WWNs which makes management a little easier, but also is susceptible to WWN spoofing which could allow access to the storage device.
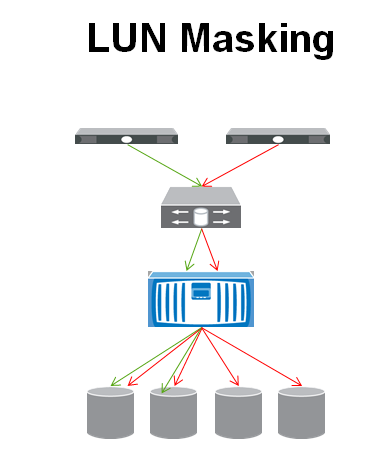
Once the zoning is done, we can further lock down access to the storage by setting up LUN (Logical Unit Number) Masking on the storage device. The SAN would prevent certain devices from seeing a specific LUN that it is hosting. This may be used more to keep a misbehaving server from accessing a LUN that it doesn’t need access to more than it is a security concern.
In the Example below we have taken a small subset of servers that are accessing one storage device. The SAN is presenting four LUNs to the server on the right side (with the red arrows) but it is only presenting two LUNs to the server on the left (with the green arrows).