vCloud Networking and Security has the capabilities to provide edge services inside of your virtual environment. Edge firewalls, network address translation, DHCP, routing are all things that vCNS Edge can do for you. This post goes into the steps necessary to deploy vCNS Edge.
I should mention that vCNS and the previous name vShield may be used interchangeably in this article.
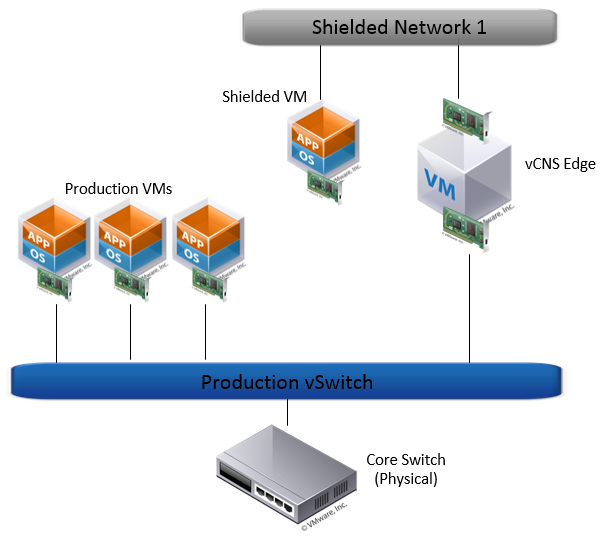
Logical Diagram
The picture below is a diagram of what our environment will look like when we’re done. We have production VMs as you might expect, and our new vCNS Edge VM. We’ve also got our new Edge network and a Shielded VM which will not be connected to the production vSwitch directly.
Deploy vCNS Edge
The first step is to have your vCNS Manager deployed. I’ve done this in a previous post, so if you haven’t done this yet, you’ll need to do this first. Remember that Edge is a component of vCNS so vCNS Manager needs to be installed first.
Now that the vCNS services are ready to go, we can deploy the edge services. Go to your vCNS portal, select your datacenter, and then go to the “Network Virtualization” tab.
Click the “+” sign to add a new edge device.
Give your new Edge Appliance a name, and description. You can also enable HA but in my environment I’m only using a single host anyway for this deployment so I’ve left it off. 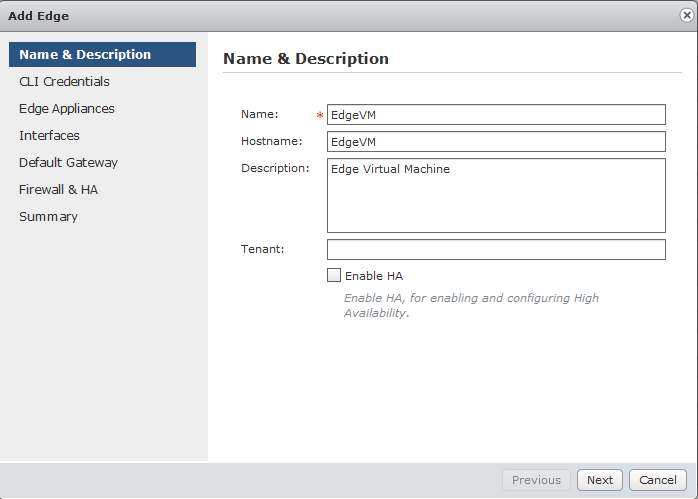
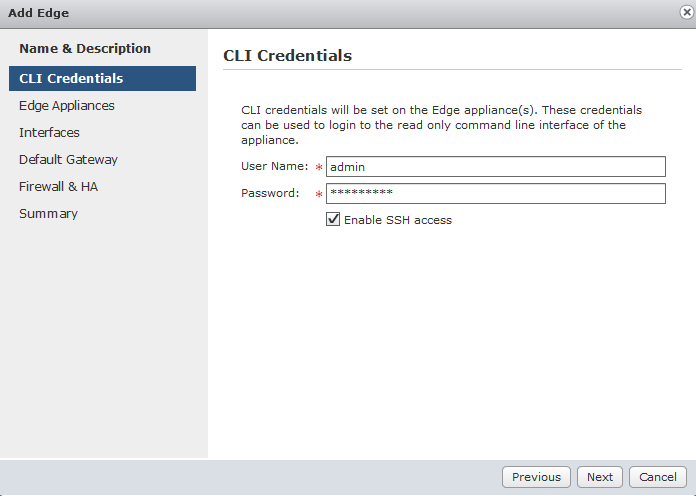
Set a password and a username for cli logins and check whether or not you want the communication to be SSH or not.
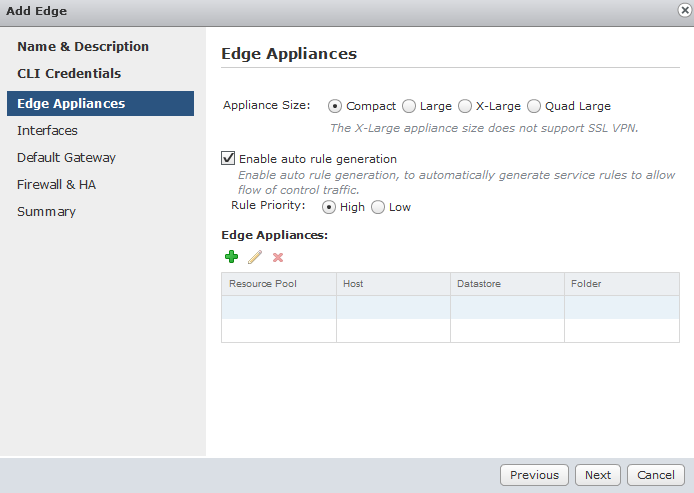
Select the size of the appliance.
The sizes of the appliance makes a difference on the capabilities. I urge you to take a look at the following VMware Blog post discussing the differences.
Also, if you’re doing this in the lab, I highly recommend the “Enable auto rule generation” to help you set your rules.
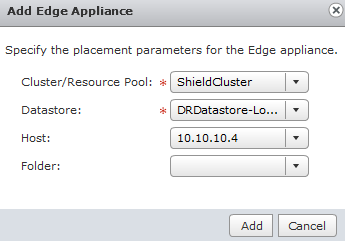
Next you’ll need to enter information about the edge appliance virtual machine. Much like and OVA deployment, you’ll need a cluster, datastore, host etc.
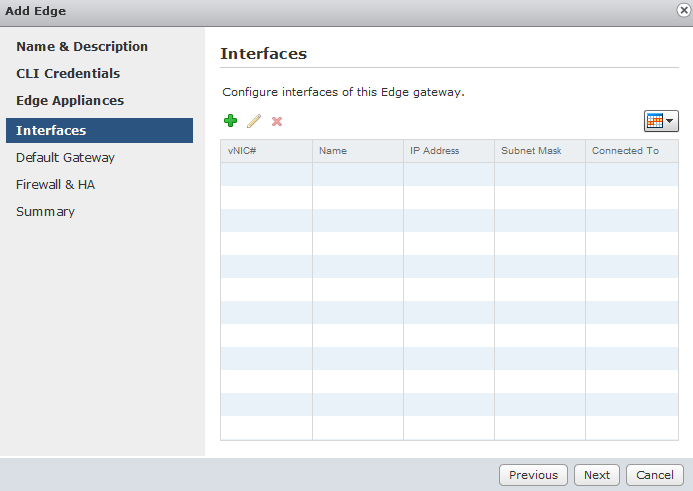
We can add up to 10 interfaces. These interfaces typically come in two forms.
1. An uplink
2. An Internal Link
Click Add
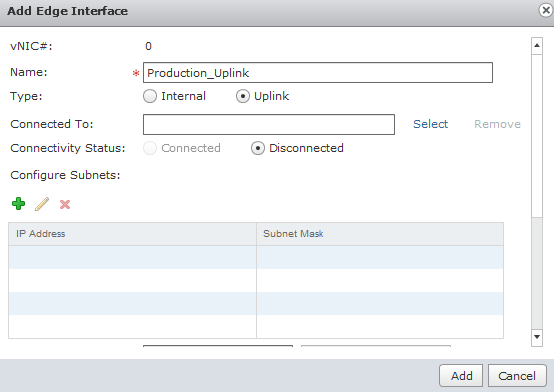
My first Nic I create my uplink. This uplink is like the default gateway and connects to my production network. Mileage may vary but this is how I’ve configured my lab. Give it a name, and select the port group this nic will be connected to.
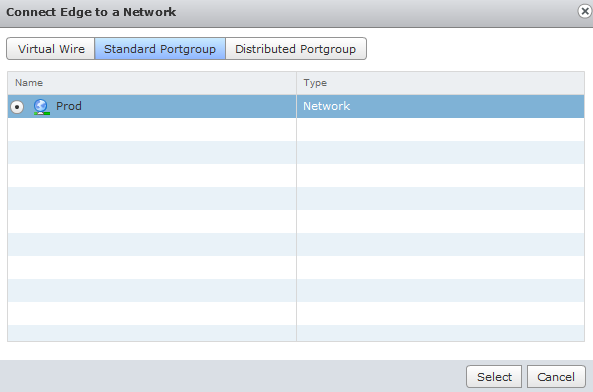
I’ve chosen the Prod port group to connect my uplink to.
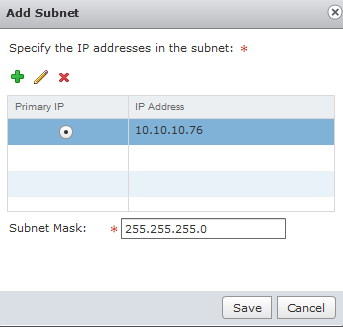
Next, you’ll need to give it an IP Address. I’ve given it an IP Address and entered a subnet mask as well.
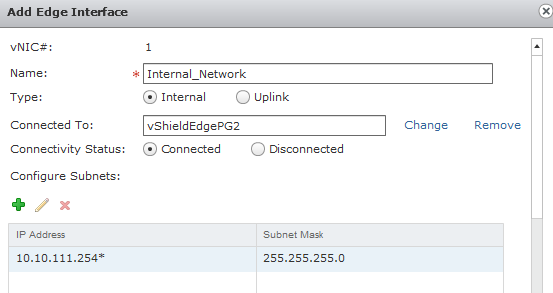
Next, I add a second nic and this time it’s an internal network. You’ll go through the same process of adding an IP Address here as well. I recommend a standardization such as x.x.x.254 for all the internal IP Addresses so that you’ll have a x.x.x.254 as the default gateway on each of the internal networks.
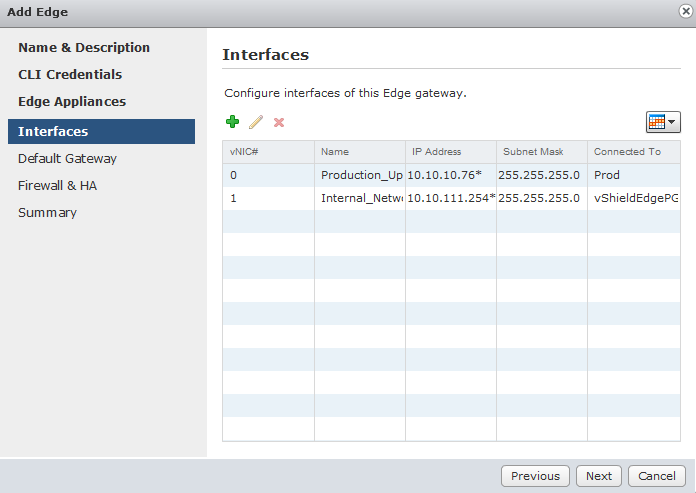
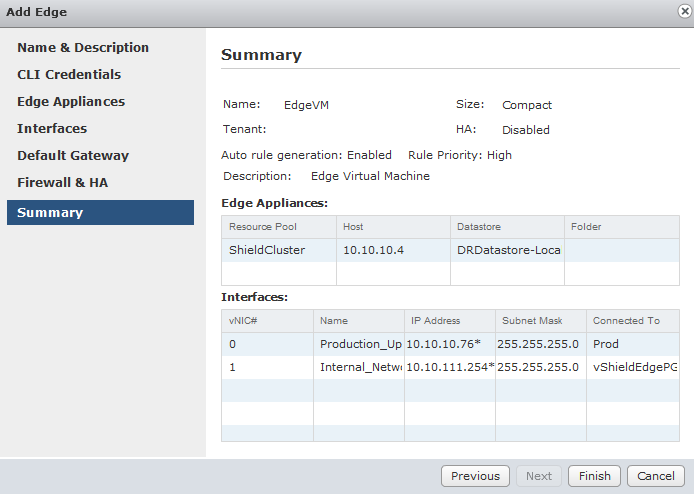
I’ve only added 1 uplink and 1 internal nic, so when I’m finished it looked something like this.
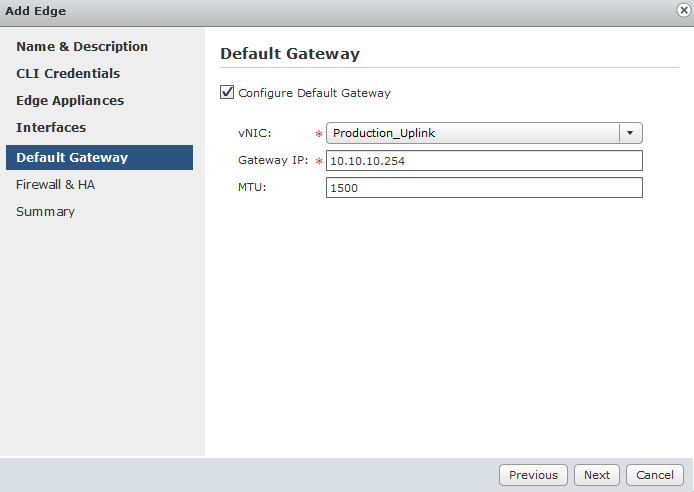
Next we configure a default gateway. I’ve selected my uplink and the IP Address of the gateway. If you’re using jumbo frames, you can change the MTU size here. Otherwise leave this alone.
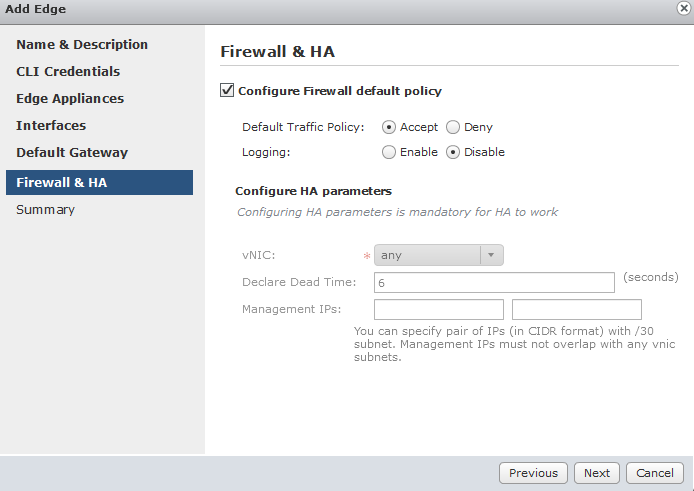
This is a lab and I’m keeping things simple. Therefore, I’m allowing all traffic through the appliance at this point. If this is a production environment, you’ll likely change this to deny and manually enter each rule for the traffic you’re going to allow.
Review the summary and click finish.
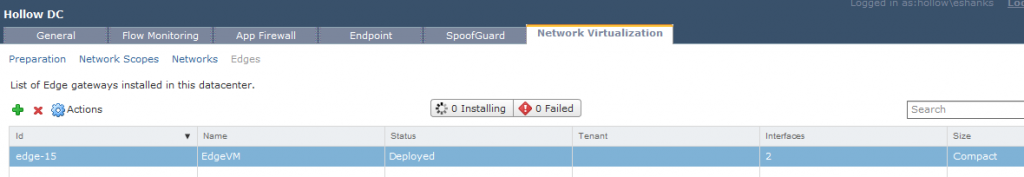
Once you click finish you’ll see the edge device being deployed.
After some time, you’ll see that it has been deployed.
Summary
Deploying the vShield Edge appliance is just the first step. Now that the edge device is available, a wealth of new opportunities are available to you which I’ll discuss further in new posts.