Congratulations, if you’ve made it this far, you’re almost done with the replacing of your VMware SSL Certificates! If you’ve followed the previous posts, you’ll know that this has been a long path to completing your goal. This post finishes installing those certificates on your vCenter server. If you missed a part please check out the previous posts to get caught up.
Congratulations, if you’ve made it this far, you’re almost done with the replacing of your VMware SSL Certificates! If you’ve followed the previous posts, you’ll know that this has been a long path to completing your goal. This post finishes installing those certificates on your vCenter server. If you missed a part please check out the previous posts to get caught up.
Create a Home Lab Certificate Authority Deploy Root Certificates via Autoenrollment Create VMware-SSL Web Certificate Template Create VMware Services Certificate Requests
Install SSL Certificates
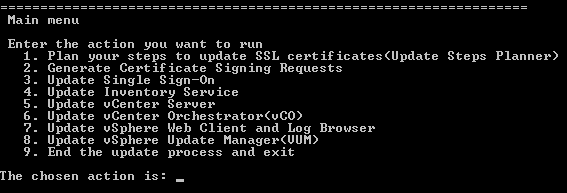
Open up the VMware SSL Automation Tool and now we can go about deploying those SSL Certificates. We’ve already completed 1 and 2, so now we need to refer to the planning steps from part 1. If you can’t remember what they are, you can re-run option 1, but be sure to copy it to notepad or something so you can keep track of where you are at.
Follow the instructions for your planning steps. This should guide you through each of the phases.
NOTE: Many of the operations you’ll perform here will stop and start VMware services. You should be prepared for this in case the server is currently being access. This will not affect any of your virtual machines, but may stop you from accessing vCenter, VUM, vCO etc.
Troubleshooting
If you are having trouble with the update proces, be sure to check to see if you are updating according to the plan. The plan may have you update a service, then update another service and then go back to the first service to register it with some other service. Follow the instructions.
Secondly, be sure that your cachain.pem files are located in the same folder as your rui.csr files etc. This is the directory that the tool is looking to find the certificates.
Thirdly, be sure that when you downloaded the certificates from your CA, you grabbed only the certificate and not the chain. See this post for additional information.
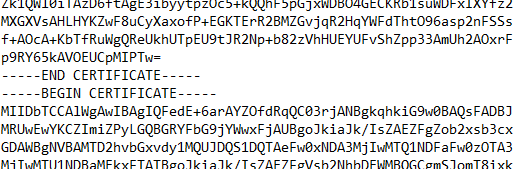
Lastly, be sure that you copied the Root64.cer file to the end of your rui.crt file, renamed it to cachain.pem and that there is no space between the two certificates.
Summary
This has been a long process, but hopefully valuable. SSL Certificates are something that shouldn’t be overlooked for an design since an untrusted certificate could mean that your environment has been compromised. It’s not a chance many corporations would want to take and hopefully the steps in this series have given you a good idea about how to replace SSL certificates for your VMware environment.