The first parts of this series focused mainly on how to install the Trend Micro Deep Security product and how to prepare your environment. This post shows you a bit more of what can be accomplished with the product.
vShield Endpoint Part 1 vSheidl Endpoint Part 2
Policies
This is the guts of the product. All the configurations you’ve done up to this point have been leading up to a solution that can help secure your environment and possibly make it comply with a regulatory body.
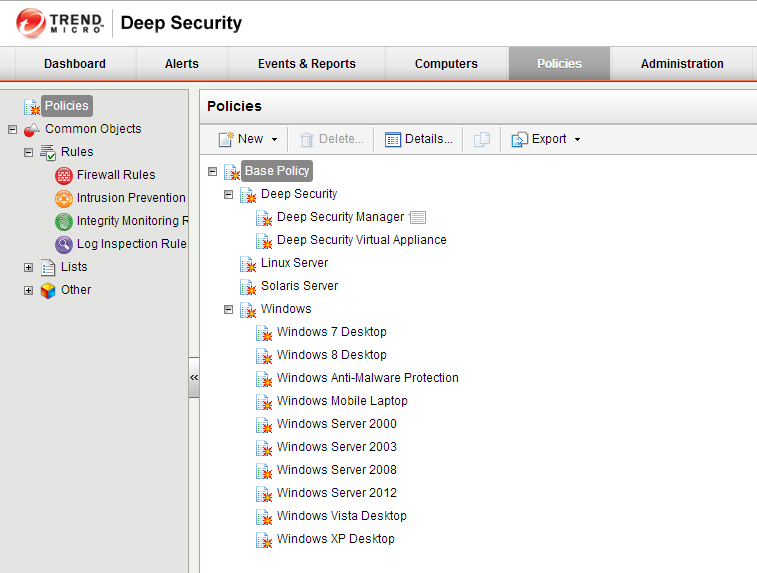
If we look at the Policies tab, we’ll see a number of Out Of The Box policies that are ready to go for a variety of Operating Systems. These base policies will give you a great start on securing your environment, but can always be tweaked to a configuration of your liking.
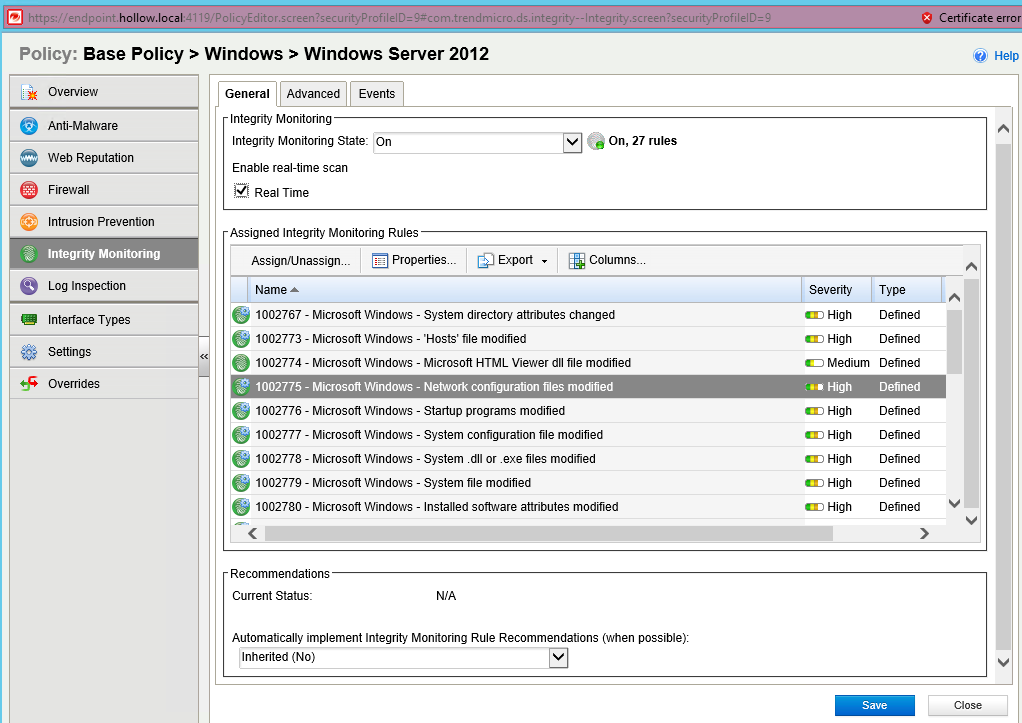
I opened the “Windows Server 2012” policy to get started. You’ll notice that you can change Firewall, IPS, Malware and log inspection policies to meet your organization’s security policies. I dove into the Integrity Monitoring section as an example.
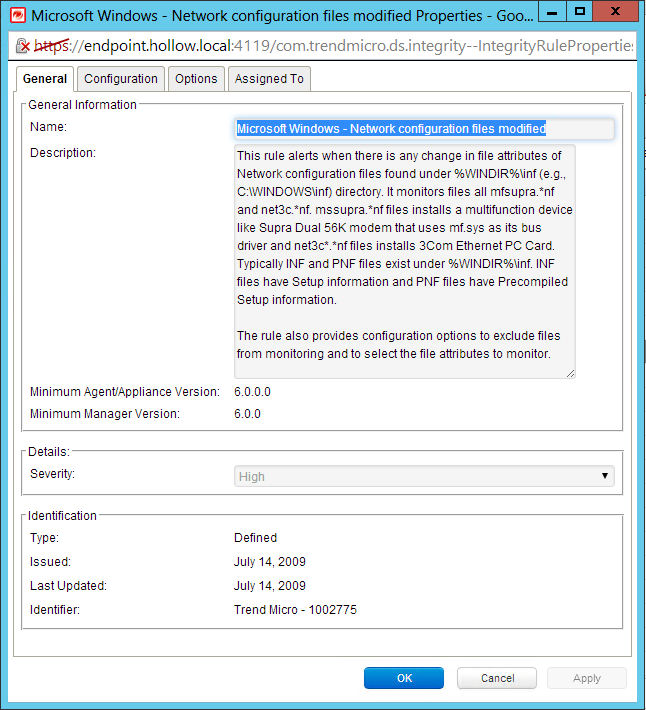
I found the “Network Configuration files modified” rule as my test. The rule can be found below, but basically it states that if I change my hosts file, I should be alerted. As a Systems Administrator this is a very valuable thing to know about because changes to host files are good sign of an attack.
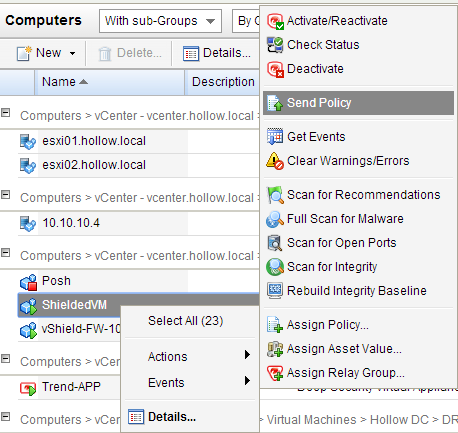
Once I’ve reviewed all the policies and modified what I needed to, the next step is to send the policy to your protected computers. Here, I’ve built a virtual machine called “ShieldedVM” for testing purposes. I have then pushed down the Server 2012 Policy to the VM.
To test things, out, I make a modification to the hosts file on the “SheildedVM” and within 5 minutes I have an alert in the “Events & Reports” tab. Pretty slick stuff here!
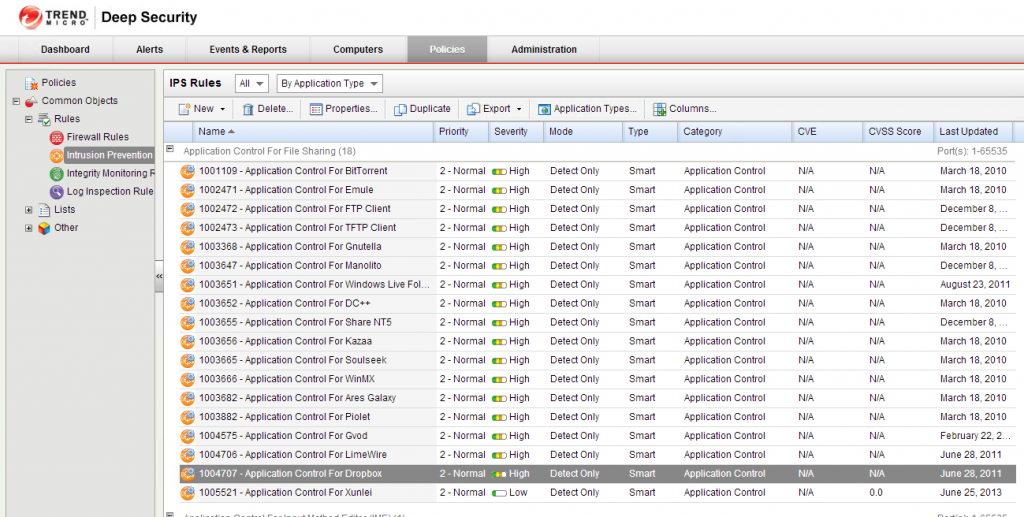
There are additional policies that can be added depending on your security requirements. The Intrusion Prevention policies allow you to use heuristics to determine traffic flows in your environment. The example below looks for dropbox traffic. NO SHADOW IT HERE!
SUMMARY
I’ve used the Trend Micro Deep Security product as an example in this series, but endpoint is available for a variety of different vendors now. As companies continue to virtualize more and more workloads, including desktops, products will continue to find new ways to protect them. Endpoint is a great way to secure traffic before it ever reaches an end user operating system.