Today, AWS announced the release of the long anticipated drift detection feature for CloudFormation. This feature has been a common feature request for many of the AWS customers that I speak with to ensure their deployments are configured as expected. This post will take you through why this is an important feature and how you can use it.
Whats the Big Deal?
If you’re not familiar with it already, CloudFormation is a free service from AWS that lets you describe your infrastructure through a YAML or JSON file and deploy the configuration. Simply define your desired state and CloudFormation will deploy the resources and arrange them so that dependent services are (usually) deployed in the right order. If you’re familiar with Ansible, Chef, or Puppet, this concept of a desired state shouldn’t be new.
As a consultant I’m often trying to drive the point home that this tool is great and some sort of IaC should be used to manage the environment. Thats usually easy at the start, but inevitably something will happen or an emergency will happen where a manual change gets made to the environment and the code doesn’t get updated. Maybe that isn’t a big deal, but what happens when someone then updates the code for another change and applies a change set. That’s right, that manual change that was made in the middle probably got wiped out and whatever issue happened before is probably back.
Introducing Drift Detection
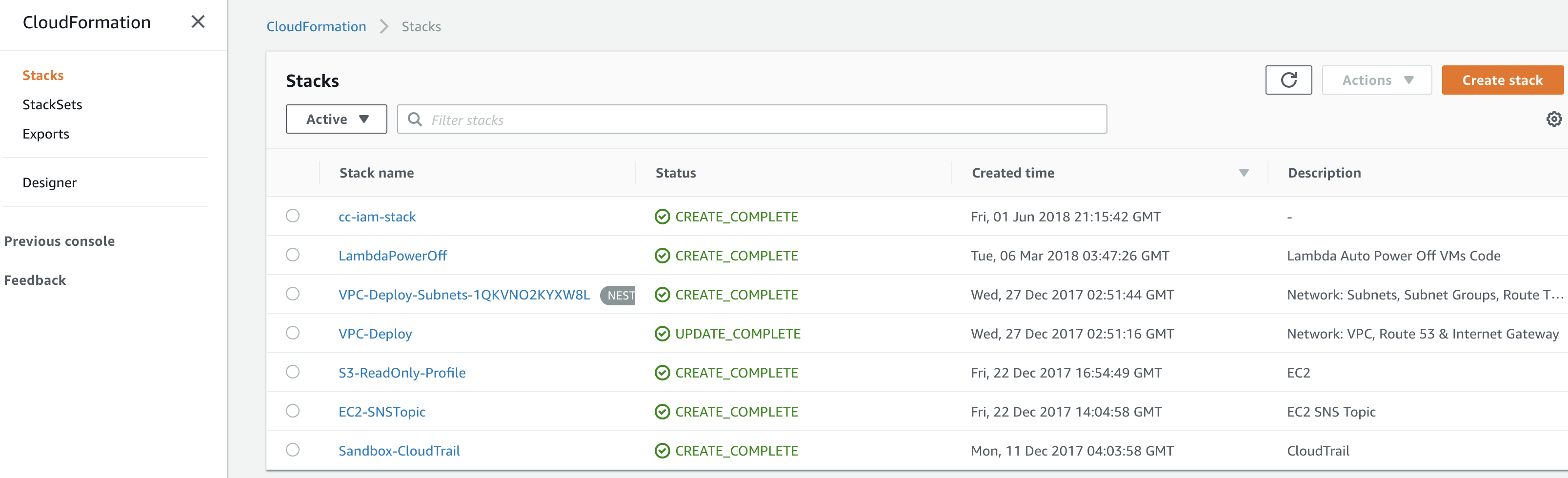
Now that the new feature has been released, lets take a look at it in a lab. The screenshot below is a list of CloudFormation templates that have been applied in one of my lab environments. Obviously, I’m always updating my infrastructure through code so I should have nothing to worry about, but lets test this new feature out anyway, just for fun.
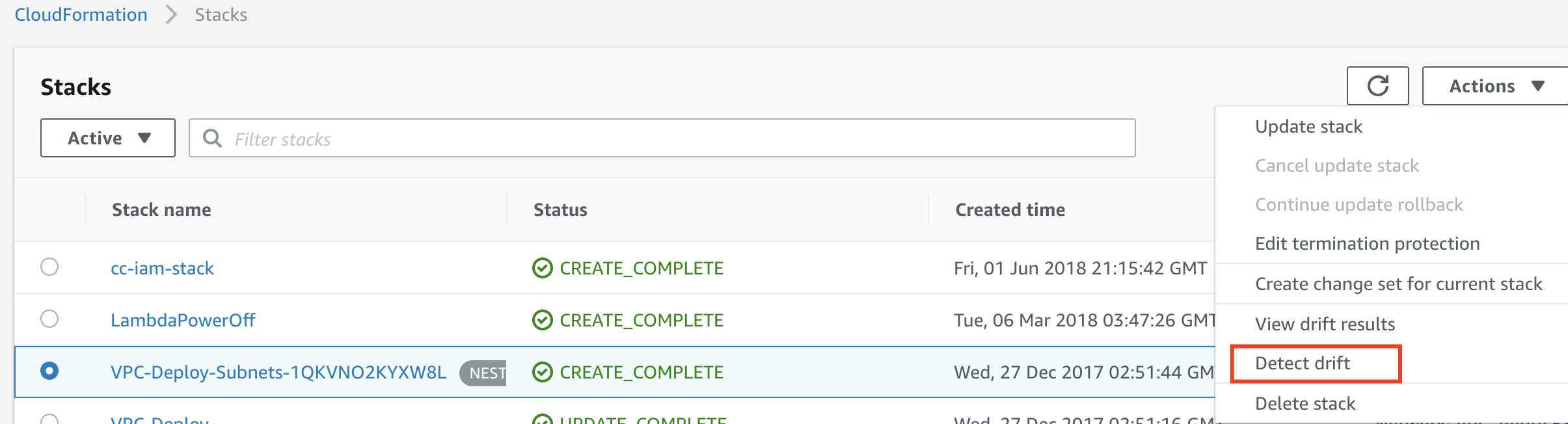
I’ve selected one of my stacks and then hit the Actions drop down and selected the “Detect Drift” option. Notice that this is also a nested stack and it will work just fine.
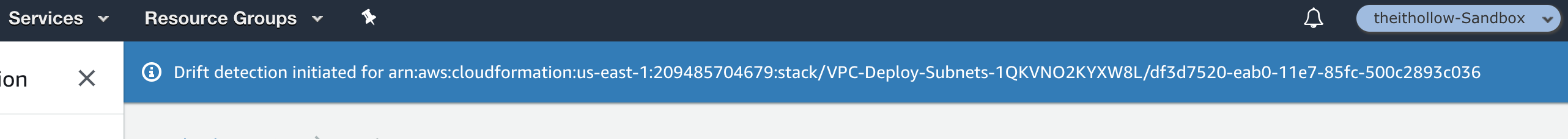
After you select “Detect drift” a notification bar will be displayed letting you know that drift detection was initiated.
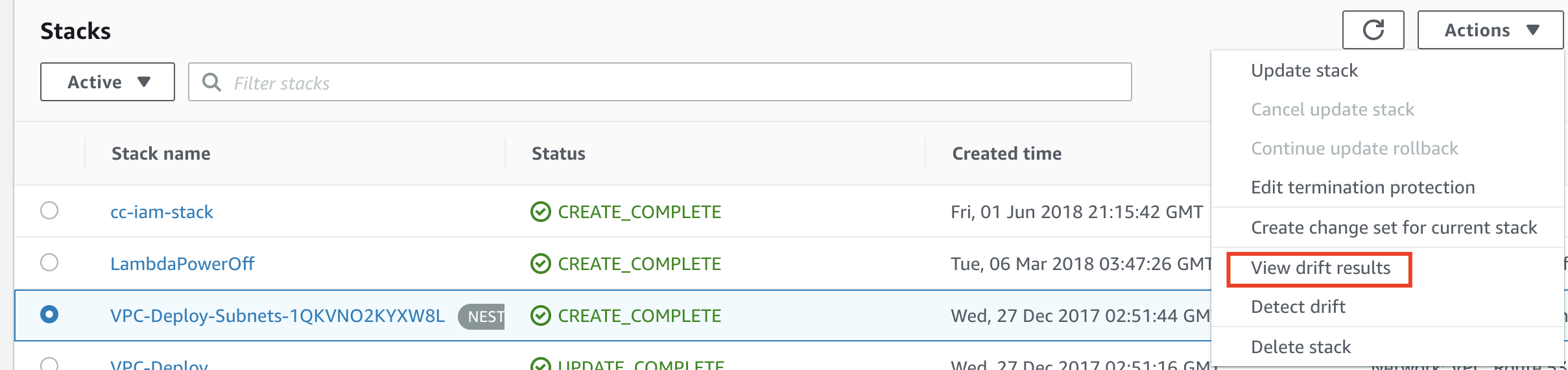
Select the stack again and then click the “View drift results” dropdown from the Action button.
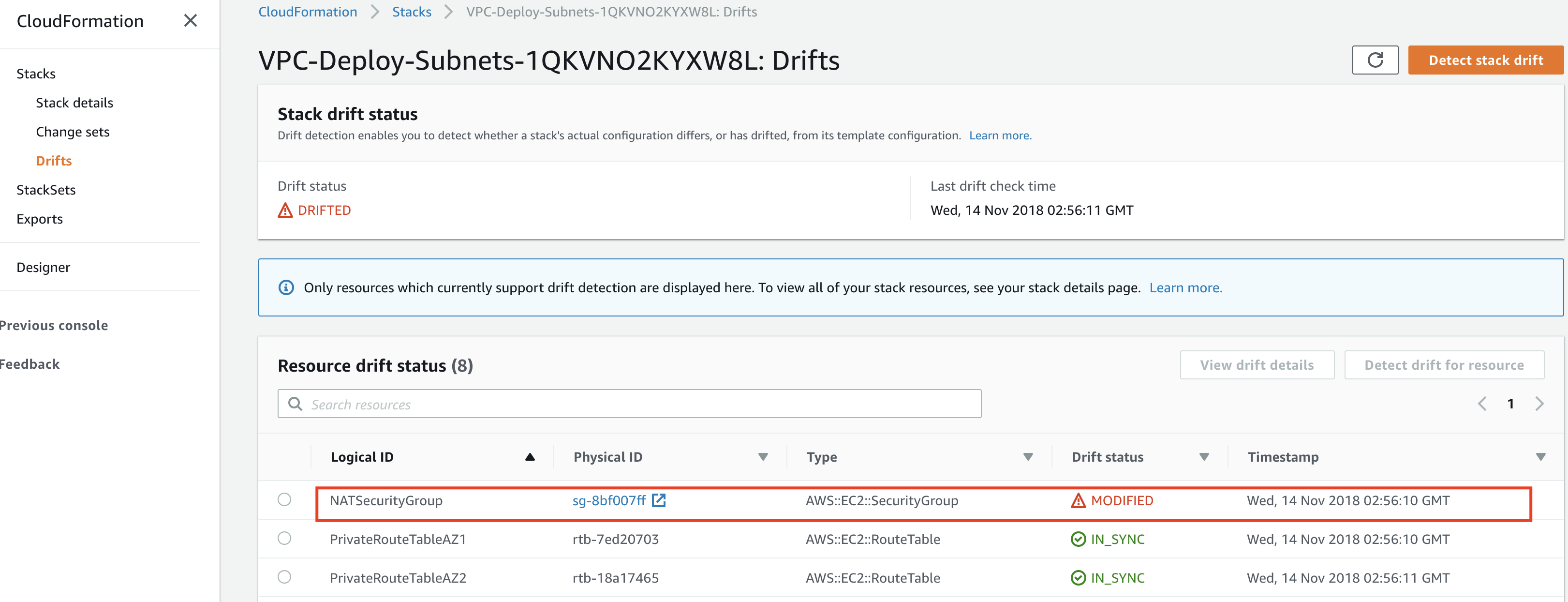
The drift detection page opens to show… wait a second! Apparently I’d made a manual change to a security group somewhere along the way and the drift detection capability has shown me what doesn’t match my template any more.
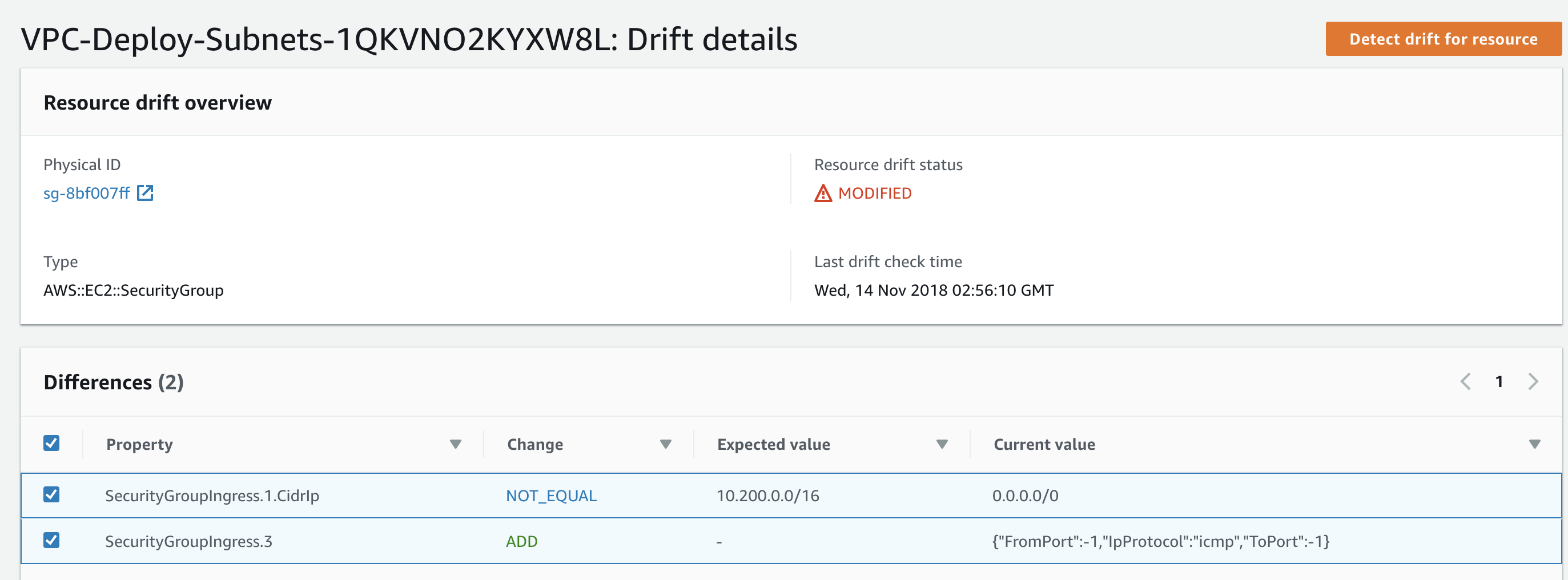
If we select the resource that has drift, we can select the “View drift details” button to get more information about the drift. As we can see from the following screen, I have replaced one of my source addresses with an anywhere (0.0.0.0/0) rule.
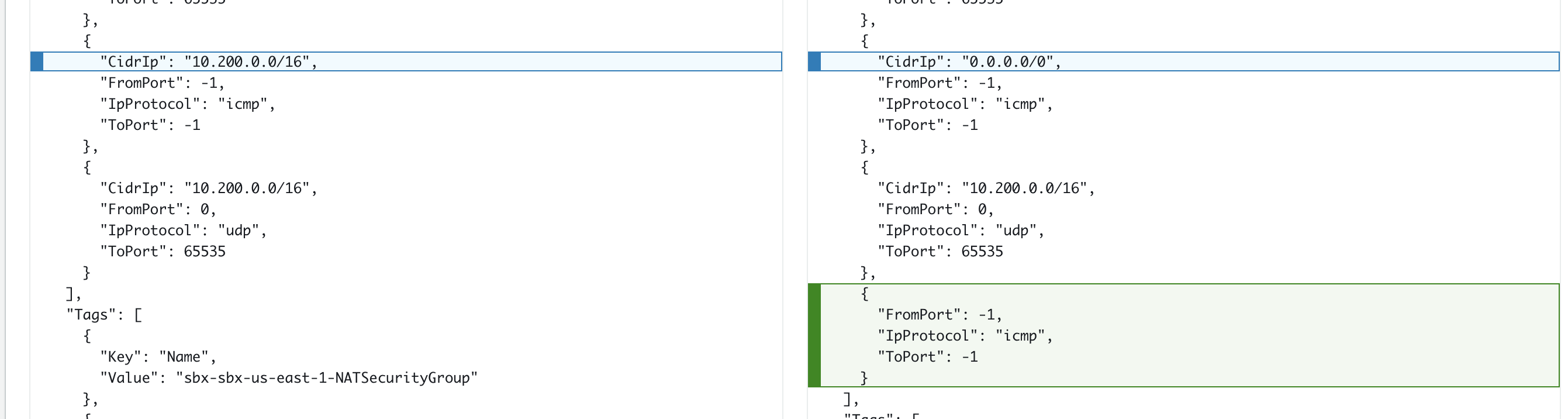
If we scroll further down, we’ll get to see the current configuration vs the template used to deploy the resource. This might be a great tool to get some manual changes that were made to the environment, into the CloudFormation templates stored in your version control repo.
Summary
CloudFormation has been a great tool to manage your AWS infrastructure and I’ve often said that it should be the only way that you interact with the AWS infrastructure. The ability to keep a desired state is enough reason to use it over the CLI or the AWS web console. Now that we can review the infrastructure with what we deployed, this tool is even more powerful. I hope you will implement drift detection as part of your AWS operations.