At AWS re:Invent this year in Las Vegas, Amazon announced a ton of services, but one that caught my eye was the AWS Resource Access Manager. This is a service that facilitates the sharing of some resources between AWS accounts so that they can be used or referenced across account boundaries. Typically, an AWS account is used as a control plane boundary (or billing boundary) between environments, but even then resources will need to communicate with each other occasionally. Now with AWS Resource Access Manager (RAM) we can shared Hosted DNS zones, Transit Gateways and other objects. This list will undoubtedly grow over time. This post will show you how you can share another new service, the AWS Transit Gateway, across multiple accounts within your organization.
Enable Resource Access Manager for your Organization
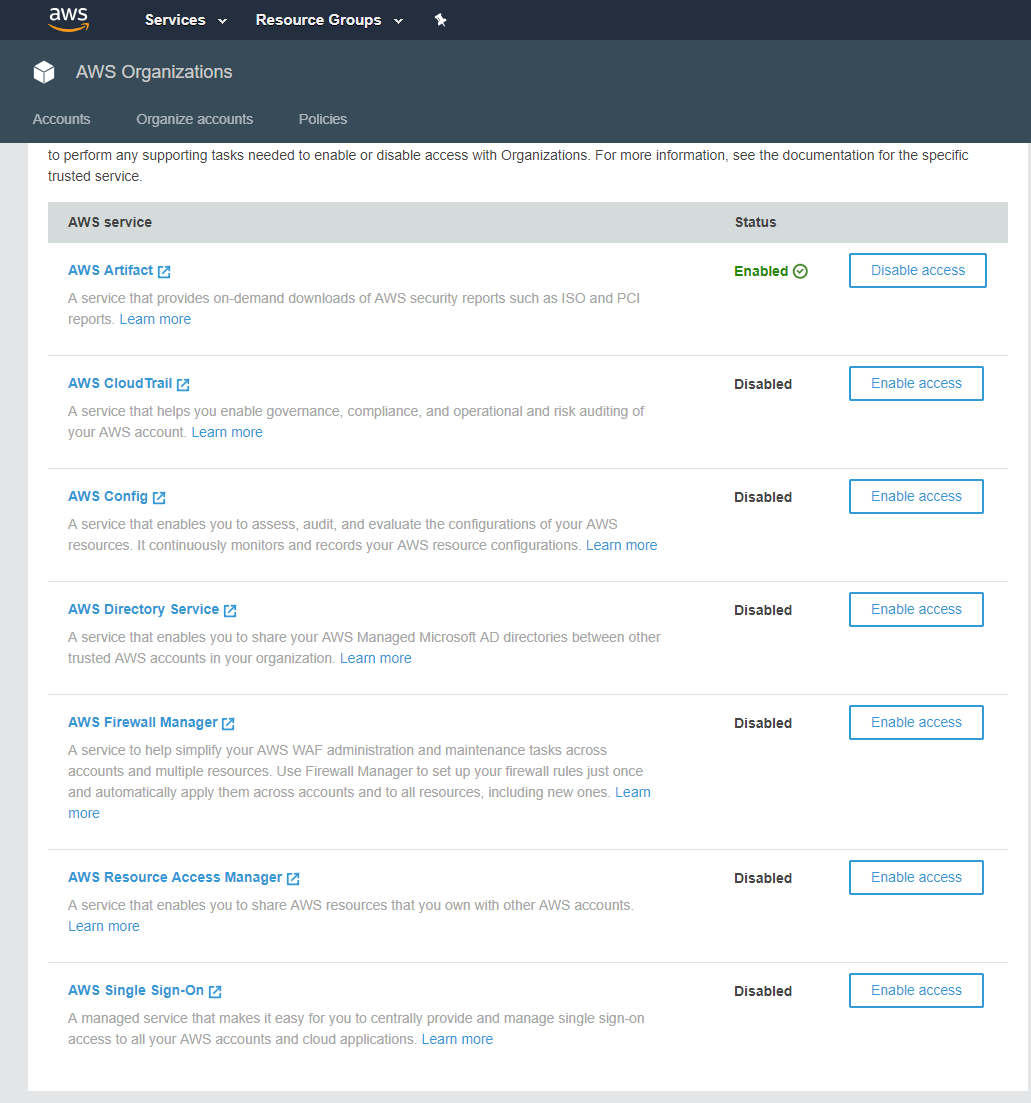
Before you can start sharing any resources in your accounts, you’ll need to login to your root account within your organization. In the organizations screen, you will have to enable the AWS Resource Access Manager by clicking the “Enable access” button.
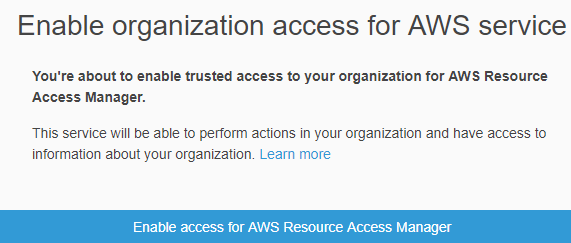
Once you click enable access, you’ll get an “are you sure” message where you’ll again need to click the “Enable access for AWS Resource Access Manager” button.
Share your Resources with Another Account
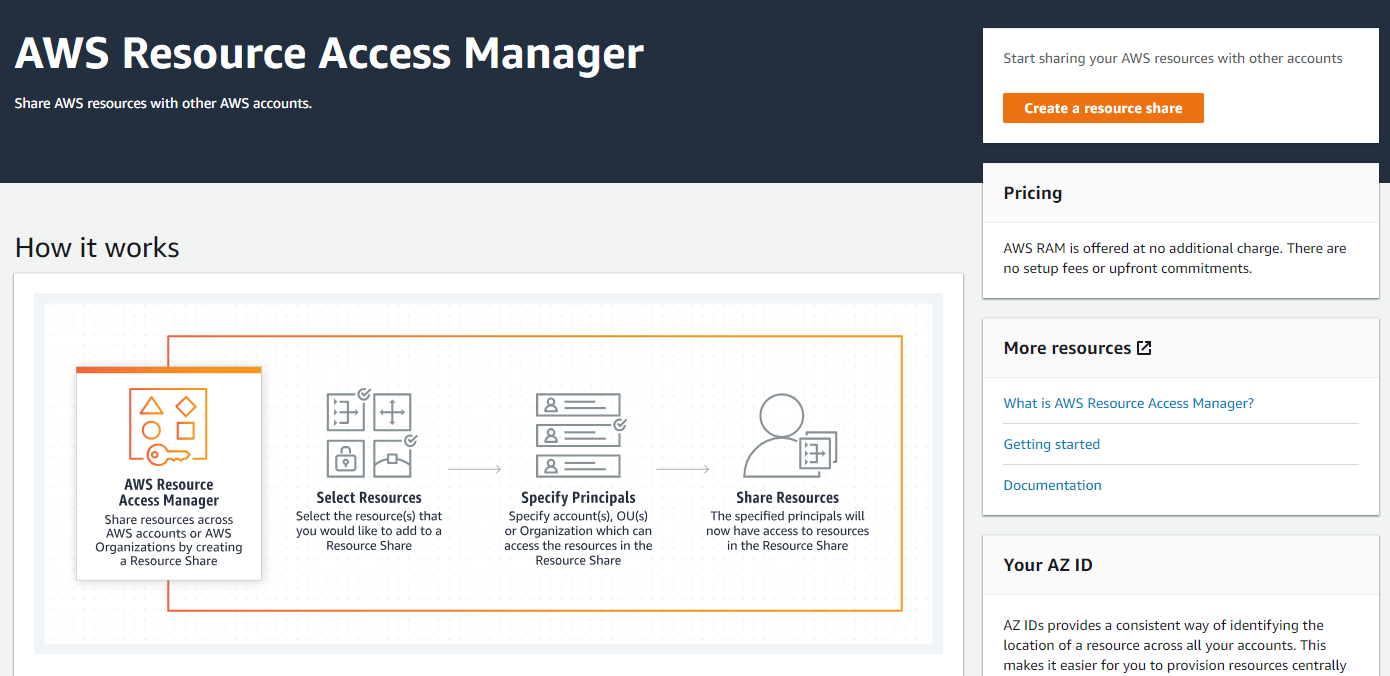
Now that you’ve enabled access to the service for your organization, you can start sharing your resources. To begin, I’ve logged into one of my accounts where I’ve created a Transit Gateway already. I want to share this Transit Gateway with another account so I can do some transitive routing between the two accounts. First, I’ll find the Resource Access Manager Service from the AWS console.
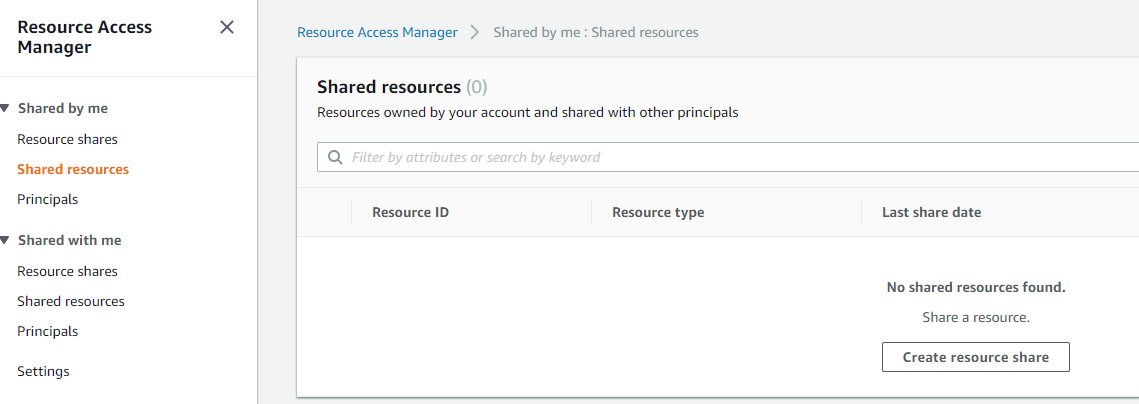
When I first login, we’ll want to go to the Shared resources menu.
Under the Shared resource menue, click the “Create resource share” button.
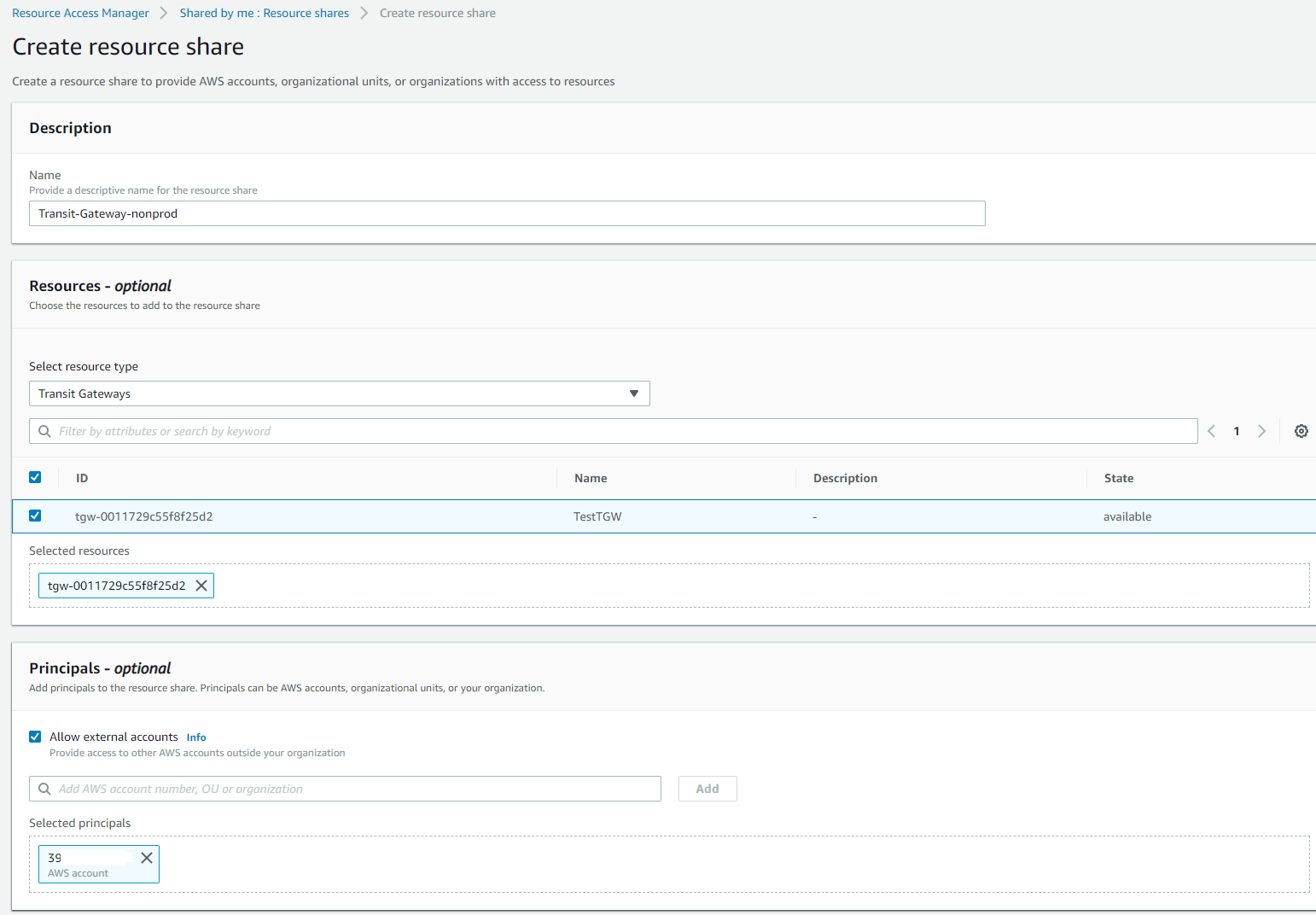
In the resource sharing screen, give the resource a name that will make it easily identifiable. Next, under the resources section, select the type of resource that you want to share. I’ve selected “Transit Gateways” and after selecting that, a list of our Transit Gateways that already exist are displayed. Select the Transit Gateway that you want to share and add it to the list of resources. Below this section, is the Principals. Here you can enter the account numbers that you wish to share the resources with, or you can also add the Organization ID so that all accounts in a specific OU or Organization are automatically shared this resource. Lastly, you can add any tags that you’d like to add for this resource share, these tags can be used for IAM permissions later if you’d like.
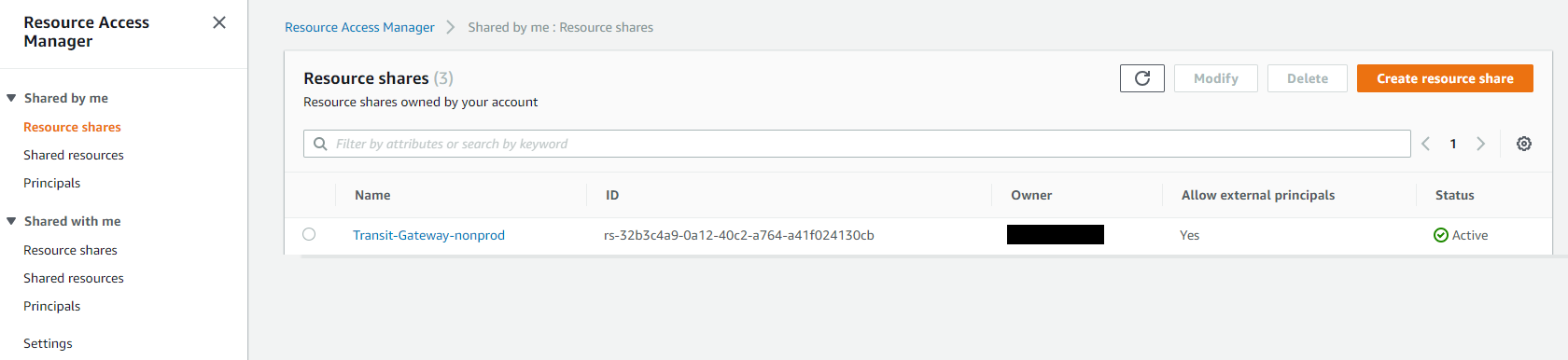
When you’re done, you’ll notice that the resource is shared with a status of Active. You’ll also see the owner (identified by account number) and whether its available to other accounts.
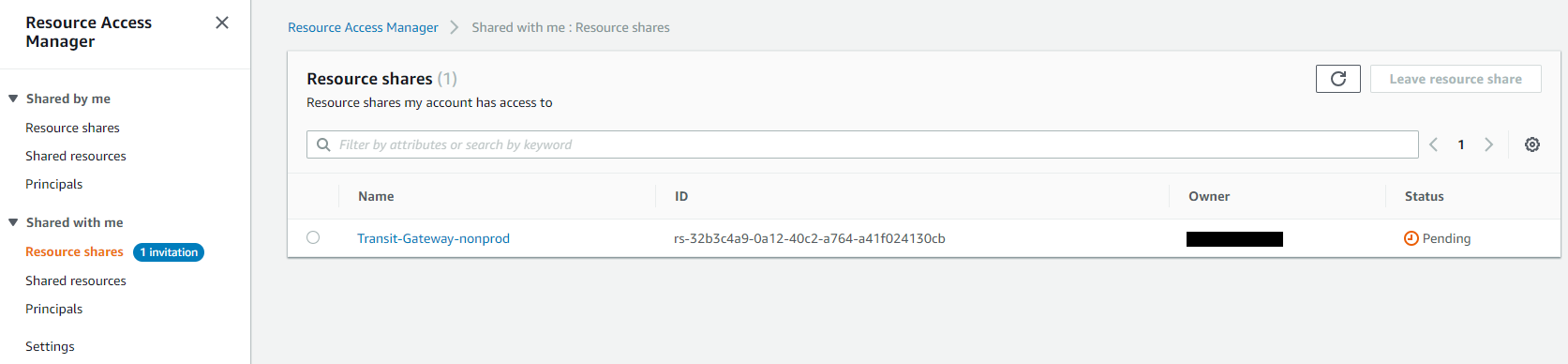
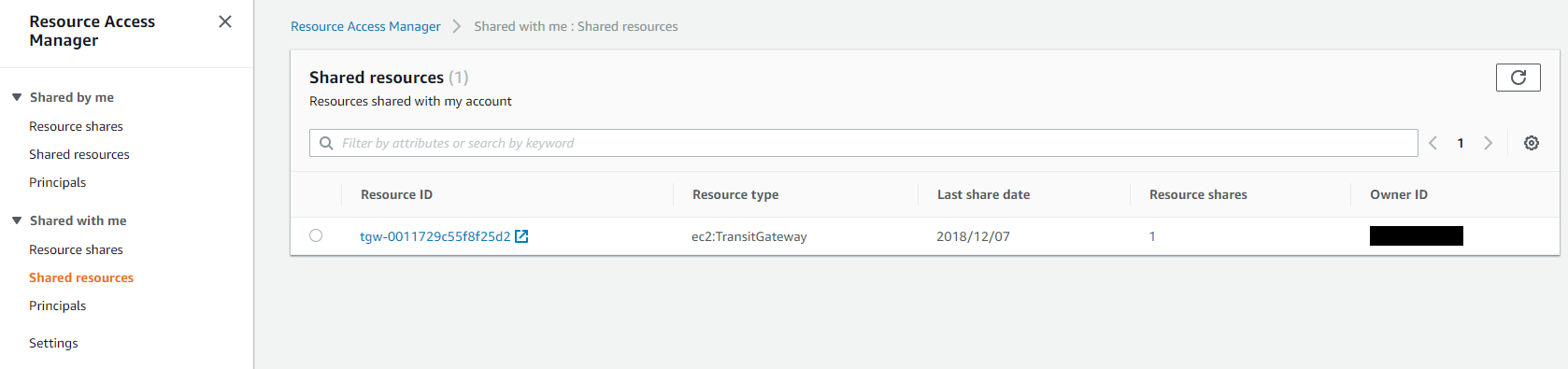
At this point, we can login to one of the other accounts where the resource has been shared. We’ll again login to the AWS Resource Access Manager and in the menu, we’ll see that under the “Shared with me” menu, we have a resource share with an invitation pending. Click on the resource that was shared.
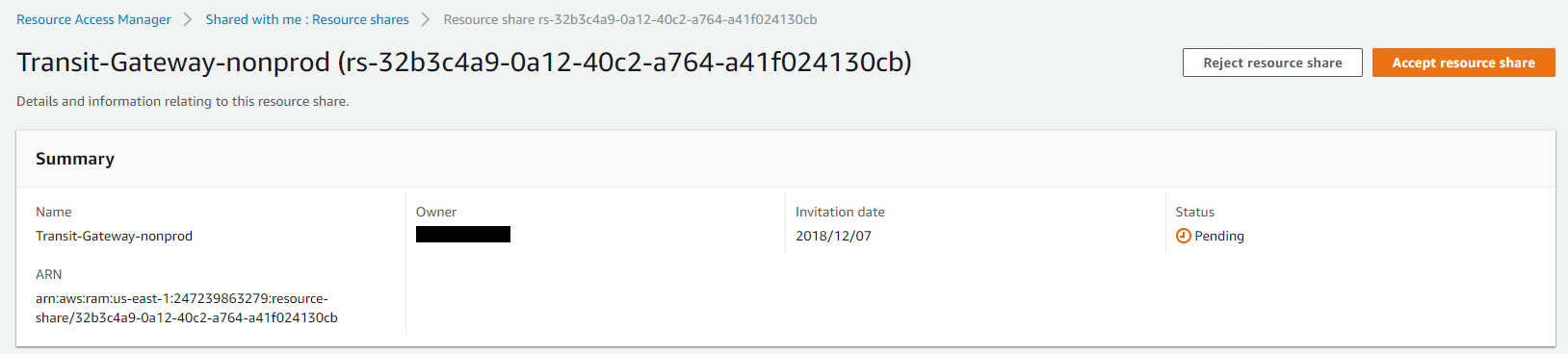
In the resource select the “Accept resource share” button to accept the sharing of this resource.
Once done, you’ll see that a resource has been shared with this account and is available for use.
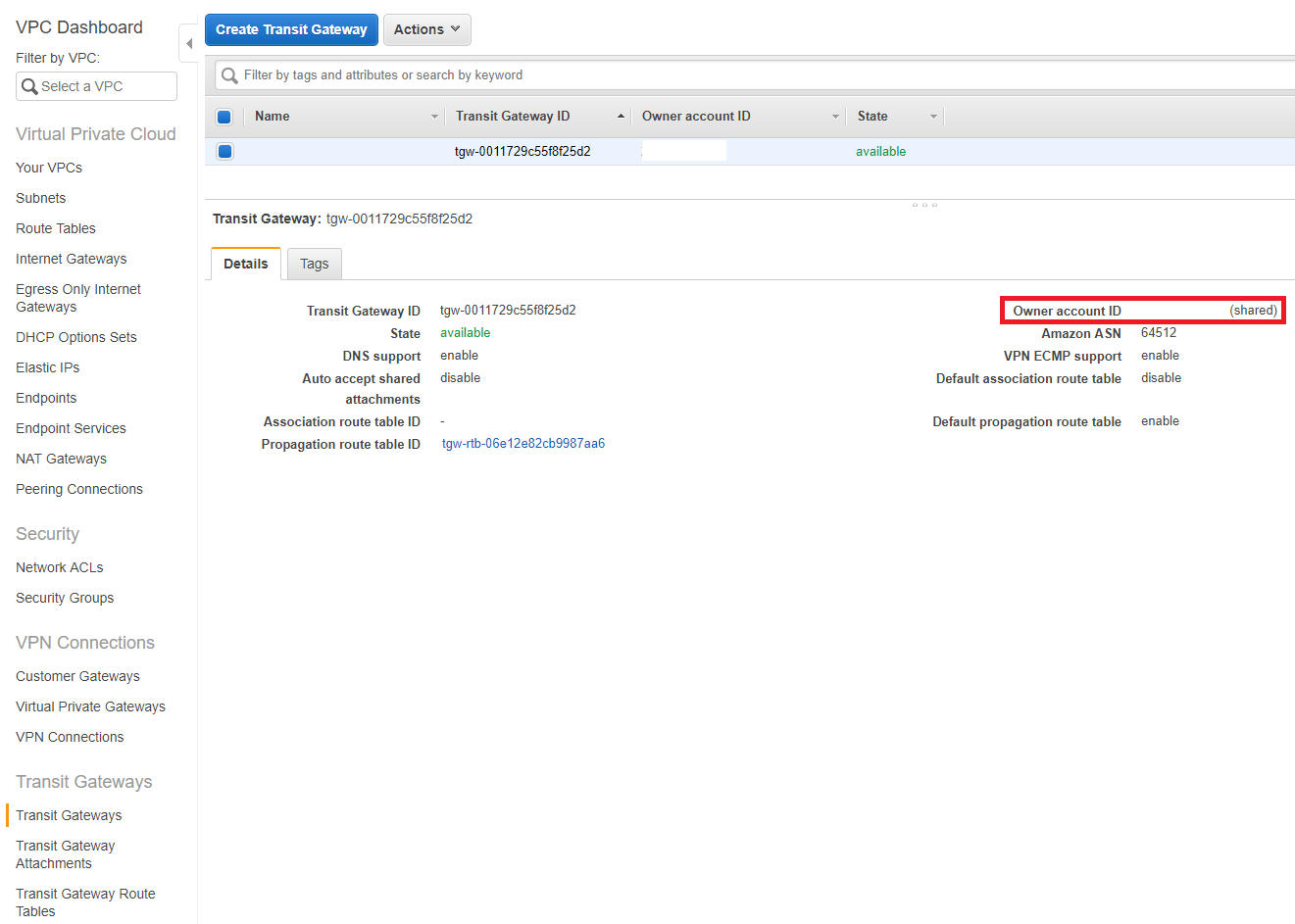
To prove that this is working, go to the area where the resource should exist if it was deployed within this account. In my case I am looking in the VPC Dashboard under Transit Gateways. I can see a Transit Gateway listed and if I select it will see that there is an Owner Account listed and that it’s shared. I can now take actions on this resource from the shared account. For example, I might add routes to this Transit Gateway from my VPC subnets.
Summary
I think we’ll see some cool things that you can do with this new service. I’m excited that we can now share resources very simply between accounts without having to use complicated IAM permissions with multiple principals listed. I expect that the list of resources that can be shared between accounts will continue to grow as this service matures.